The Canadian Privacy Law Blog: Developments in privacy law and writings of a Canadian privacy lawyer, containing information related to the Personal Information Protection and Electronic Documents Act (aka PIPEDA) and other Canadian and international laws.
Recent Posts
- This blog has moved
- Some thoughts on street photography
- RCMP changes rules for criminal records checks
- Saskatchewan amends privacy regs to permit solicia...
- US Federal judge declares warrantless wiretapping ...
- Commisser releases discussion paper on cloud compu...
- Heathrow worker given police warning for body scan...
- How Privacy Vanishes Online, a Bit at a Time
- Facebook plans to allow users to "share" location
- Drawing the curtain on ISP cooperation with law en...
On Twitter
About this page and the author
 The author of this blog,
David T.S. Fraser, is a Canadian privacy lawyer who practices with the
firm of McInnes Cooper. He is the author of the Physicians' Privacy Manual. He has a national and international practice advising corporations and individuals on matters related to Canadian privacy laws.
The author of this blog,
David T.S. Fraser, is a Canadian privacy lawyer who practices with the
firm of McInnes Cooper. He is the author of the Physicians' Privacy Manual. He has a national and international practice advising corporations and individuals on matters related to Canadian privacy laws.
For full contact information and a brief bio, please see David's profile.
Please note that I am only able to provide legal advice to clients. I am not able to provide free legal advice. Any unsolicited information sent to David Fraser cannot be considered to be solicitor-client privileged.
Privacy Calendar
Archives
- January 2004
- February 2004
- March 2004
- April 2004
- May 2004
- June 2004
- July 2004
- August 2004
- September 2004
- October 2004
- November 2004
- December 2004
- January 2005
- February 2005
- March 2005
- April 2005
- May 2005
- June 2005
- July 2005
- August 2005
- September 2005
- October 2005
- November 2005
- December 2005
- January 2006
- February 2006
- March 2006
- April 2006
- May 2006
- June 2006
- July 2006
- August 2006
- September 2006
- October 2006
- November 2006
- December 2006
- January 2007
- February 2007
- March 2007
- April 2007
- May 2007
- June 2007
- July 2007
- August 2007
- September 2007
- October 2007
- November 2007
- December 2007
- January 2008
- February 2008
- March 2008
- April 2008
- May 2008
- June 2008
- July 2008
- August 2008
- September 2008
- October 2008
- November 2008
- December 2008
- January 2009
- February 2009
- March 2009
- April 2009
- May 2009
- June 2009
- July 2009
- August 2009
- September 2009
- October 2009
- November 2009
- December 2009
- January 2010
- February 2010
- March 2010
- April 2010
Links


Blogs I Follow
Small Print
The views expressed herein are solely the author's and should not be attributed to his employer or clients. Any postings on legal issues are provided as a public service, and do not constitute solicitation or provision of legal advice. The author makes no claims, promises or guarantees about the accuracy, completeness, or adequacy of the information contained herein or linked to. Nothing herein should be used as a substitute for the advice of competent counsel.
This web site is presented for informational purposes only. These materials do not constitute legal advice and do not create a solicitor-client relationship between you and David T.S. Fraser. If you are seeking specific advice related to Canadian privacy law or PIPEDA, contact the author, David T.S. Fraser.
Tuesday, July 31, 2007
Facebook security glitch exposes user in-boxes
Facebook apparently has been having a bit of a tough time in the uptime department. And a glitch of some sort has resulting in users being served the wrong inbox. Not a happy event for one of the hottest web properties. See: Facebook security glitch exposes user in-boxes | The Register.
Labels: facebook, privacy, social networking
Cartoon: It's private
This is the oldest joke in the privacy business, but privacy cartoons are rare so this merits a mention:
Going postal over privacy
This is very interesting ....
Worker: Postal Service sold private data on Yahoo! NewsBy GENE JOHNSON, Associated Press Writer
Mon Jul 30, 11:08 PM ET
A Postal Service employee sued the agency Monday, accusing it of selling the personal information of its workers to credit card and other companies without consent.
Lance McDermott, a mechanic for mail-processing equipment, said in the complaint in U.S. District Court that he has been inundated with credit card, cell phone and life insurance offers in the past two years.
In some instances, it appears the agency provided the companies with eight-digit employee identification numbers, used for sensitive tasks such as accessing health care records, the complaint said.
McDermott said he was deluged with offers from Visa, Sprint Nextel Corp. and other companies.
The lawsuit seeks class-action status on behalf of other Postal Service workers, the return of any money the agency may have made by violating the federal Privacy Act, and other damages.
An agency spokesman in Seattle said he could not immediately comment.
"His major concern is that he doesn't want to take the risk that his personal information is going to be released to a third party and be subject to identity theft," McDermott's lawyer, Steve Berman, said. "And he doesn't think his employer should be benefiting from his personal information without his permission."
Berman said he does not know how much the companies may have paid the Postal Service for access to its "master file" of employee information. Nearly 800,000 people work for the agency, he said.
McDermott's complaint cited the Postal Service's April 2005 "Guidelines for Privacy" handbook, which included a section on direct marketing to workers: "Growing revenue is a critical strategy for the Postal Service," it said, and for that reason, the agency would allow companies to bid for the right to mail promotional offers to Postal Service workers. The offers arrive "cobranded" with the Postal Service's logo.
While employees could choose not to have their information forwarded to other companies, the policy still violated the Privacy Act by releasing data to companies without explicit permission from the employees, the complaint said.
With few exceptions, the law forbids federal agencies from releasing personal information of employees without consent.
Representatives of Visa and Sprint Nextel did not immediately return calls seeking comment.
Labels: health information, identity theft, privacy
Monday, July 30, 2007
Cedars Sinai reserves the right to disclose your personal info ....
This is pretty amazing. Cory Doctorow of Boing Boing! has posted a picture of a notice received from Cedars Sinai hospital, providing the purposes for which patients' health information may be disclosed.
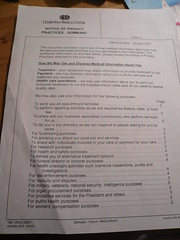
The purposes include "Protective services for the President and [unnamed] others", and "national security, intelligence purposes".
Originally uploaded by gruntzooki, via Boing Boing. And thanks to Rob Hyndman for pointing me to it....
Labels: health information, national security, privacy
Blawgworld 2007
 The 2007 edition of Technolawyer's Blawgworld is being released today. (Download the hefty PDF file here.) I've had the benefit of a sneak preview and it's quite a compilation of the best posts from the top legal blogs. I'm particularly impressed that so many leading Canadian blogs are not only on their radar, but are front and centre.
The 2007 edition of Technolawyer's Blawgworld is being released today. (Download the hefty PDF file here.) I've had the benefit of a sneak preview and it's quite a compilation of the best posts from the top legal blogs. I'm particularly impressed that so many leading Canadian blogs are not only on their radar, but are front and centre.
It includes this blog, Michael Geist's, David Canton's, Slaw and others. Be sure to check it out.
Labels: privacy
Friday, July 27, 2007
Quebec Movie Chain Sued Over "Abusive" Search
Michael Geist is blogging about a recent lawsuit filed in Quebec over searches of theatre patrons, apparently looking for camcording equipment. As Michael notes: "Bill C-59, the new anti-camcording law, creates new penalties for camcording, but does not grant theatre owners any new rights to search patrons."
Check it out: Michael Geist - Quebec Movie Chain Sued Over "Abusive" Search.
Labels: privacy
Privacy on parade in the UK
The Lawyer.com has an interesting article on the use of the Human Rights Act in the United Kingdom to dramatically extend individual privcy rights. It also includes a brief overview of some significant cases:
Privacy on parade - 16 July 2007Five key cases
Lord Browne v Associated Newspapers, 2007
Eady J decided BP's shareholders had the right to know that Lord Browne had lied in court. But what they did not need to know were details of his personal conversations with ex-boyfriend Jeff Chevalier, which remain private.
McKennitt v Ash, 2005
One of the first real tests of Article 8. Eady J went through a number of passages from an exposé of singer Loreena McKennitt, deciding on each one whether it breached privacy rules. The result? A win for privacy.
Prince of Wales v Associated Newspapers, 2006
Blackburne J weighed up Articles 8 and 10 of the Human Rights Act and found that the former was stronger than the latter in the case of publishing the prince's diary.
Douglas v Hello!, 2007
The Lords' decision on Douglas has given celebrities greater control over their images and the way they are portrayed in the press.
Campbell v MGN, 2004
The Lords found that the photographs of Naomi Campbell attending a Narcotics Anonymous meeting had a far greater effect than just words and so had invaded her privacy.
Snooping on electronic health records
While electronic health records make it easier for employees to snoop on medical records, they also make it easier to catch them. The numbers of employees suspended from this particular clinc for snooping is rather staggering:
Park Nicollet gets tough on snooping in patient filesMore than 100 Park Nicollet Clinic employees have been suspended this year for violating federal laws on patient privacy -- mostly by tapping into electronic records of relatives or friends, according to clinic officials.
This week, the clinic notified its 8,300 employees about the suspensions as a reminder of what it calls its "zero tolerance policy" on confidentiality. Already, twice as many employees have been disciplined for privacy violations in 2007 than in all of 2006, officials say. They were suspended without pay for three days.
The problem has surfaced in hospitals and clinics across the nation as they have switched to electronic records. While new technology has made it easier for employees to snoop where they don't belong, experts say, it has also made it easier to catch them....
Labels: privacy
Former privacy commissioner named as Ontario's conflict of interest commissioner
Ontario's first Information and Privacy Commissioner, Sidney Linden, has been named as Ontario's Conflict of Interest Commissioner: CANOE -- CNEWS - Canada: New Ont. conflict of interest commissioner named.
Labels: privacy
Tuesday, July 24, 2007
Google pulls back cookie expiry dates
In another privacy move, Google is changing the expiry date on their cookies to 24 months. See: Official Google Blog: Cookies: expiring sooner to improve privacy.
The "but I've got nothing to hide" argument
Daniel Solove, at the University of George Washtington School of Law, has written an interesting article on the "But I've got nothing to hide." Here's a link to the download site and the introduction:
SSRN-'I've Got Nothing to Hide' and Other Misunderstandings of Privacy by Daniel SoloveINTRODUCTION
Since the September 11 attacks, the government has been engaging in extensive surveillance and data mining. Regarding surveillance, in December 2005, the New York Times revealed that after September 11, the Bush Administration secretly authorized the National Security Administration (NSA) to engage in warrantless wiretapping of American citizens’ telephone calls.2 As for data mining, which involves analyzing personal data for patterns of suspicious behavior, the government has begun numerous programs. In 2002, the media revealed that the Department of Defense was constructing a data mining project, called “Total Information Awareness” (TIA), under the leadership of Admiral John Poindexter. The vision for TIA was to gather a variety of information about people, including financial, educational, health, and other data. The information would then be analyzed for suspicious behavior patterns. According to Poindexter: “The only way to detect . . . terrorists is to look for patterns of activity that are based on observations from past terrorist attacks as well as estimates about how terrorists will adapt to our measures to avoid detection.”3 When the program came to light, a public outcry erupted, and the U.S. Senate subsequently voted to deny the program funding, ultimately leading to its demise. Nevertheless, many components of TIA continue on in various government agencies, though in a less systematic and more clandestine fashion.4
In May 2006, USA Today broke the story that the NSA had obtained customer records from several major phone companies and was analyzing them to identify potential terrorists.5 The telephone call database is reported to be the “largest database ever assembled in the world.”6 In June 2006, the New York Times reported that the U.S. government had been accessing bank records from the Society for Worldwide Interbank Financial Transactions (SWIFT), which handles financial transactions for thousands of banks around the world.7 Many people responded with outrage at these announcements, but many others did not perceive much of a problem. The reason for their lack of concern, they explained, was because: “I’ve got nothing to hide.”
The argument that no privacy problem exists if a person has nothing to hide is frequently made in connection with many privacy issues. When the government engages in surveillance, many people believe that there is no threat to privacy unless the government uncovers unlawful activity, in which case a person has no legitimate justification to claim that it remain private.
Thus, if an individual engages only in legal activity, she has nothing to worry about. When it comes to the government collecting and analyzing personal information, many people contend that a privacy harm exists only if skeletons in the closet are revealed. For example, suppose the government examines one’s telephone records and finds out that a person made calls to her parents, a friend in Canada, a video store, and a pizza delivery shop. “So what?” that person might say. “I’m not embarrassed or humiliated by this information. If anybody asks me, I’ll gladly tell them what stores I shop at. I have nothing to hide.”
The “nothing to hide” argument and its variants are quite prevalent in popular discourse about privacy. Data security expert Bruce Schneier calls it the “most common retort against privacy advocates”8 Legal scholar Geoffrey Stone refers to it as “all-too-common refrain.”9 The “nothing to hide” argument is one of the primary arguments made when balancing privacy against security. In its most compelling form, it is an argument that the privacy interest is generally minimal to trivial, thus making the balance against security concerns a foreordained victory for security. Sometimes the “nothing to hide” argument is posed as a question: “If you have nothing to hide, then what do you have to fear?” Others ask: “If you aren’t doing anything wrong, then what do you have to hide?”
In this essay, I will explore the “nothing to hide” argument and its variants in more depth. Grappling with the “nothing to hide” argument is important, as the argument reflects the sentiments of a wide percentage of the population. In popular discourse, the “nothing to hide” argument’s superficial incantations can readily be refuted. But when the argument is made in its strongest form, it is far more formidable.
In order to respond to the “nothing to hide” argument, it is imperative that we have a theory about what privacy is and why it is valuable. At its core, the “nothing to hide” argument emerges from a conception of privacy and its value. What exactly is “privacy”? How valuable is privacy and how do we assess its value? How do we weigh privacy against countervailing values? These questions have long plagued those seeking to develop a theory of privacy and justifications for its legal protection. This essay begins in Part I by discussing the “nothing to hide” argument. First, I introduce the argument as it often exists in popular discourse and examine frequent ways of responding to the argument. Second, I present the argument in what I believe to be its strongest form. In Part II, I briefly discuss my work thus far on conceptualizing privacy. I explain why existing theories of privacy have been unsatisfactory, have led to confusion, and have impeded the development of effective legal and policy responses to privacy problems. In Part III, I argue that the “nothing to hide” argument—even in its strongest form—stems from certain faulty assumptions about privacy and its value. The problem, in short, is not with finding an answer to the question: “If you’ve got nothing to hide, then what do you have to fear?” The problem is in the very question itself.
Labels: health information, privacy, schneier, surveillance
Friday, July 20, 2007
Ask.com promises not to keep query data
While Ask.com is not at the top of the heap of search engines, I think this is an interesting development. Ask.com announced today that it will not store users' queries. What I find most interesting is this observation:
"The number of people this is important to is small," said Doug Leeds, Ask's vice president of product management. "But to these people, it's very important."
This has been my experience. Despite polls and surveys, people who truly care about privacy are a minority. But it seems to be a growing minority and it isn't black and white. And within that segment is a group that cares about privacy a lot. There are also degrees of privacy interest and many people will use privacy characteristics of a service as a distinguishing feature between products or services. It makes sense to address that group of potential customers.
Camera metadata may lead to Harry Potter leaker
Last year I blogged about the metadata created by cameras that could unintentionally reveal information (Canadian Privacy Law Blog: Beware of hidden digital camera metadata). EXIF data is in the news again...
A little while ago, someone released the new Harry Potter book in the form of photographs of each page. The person who did this didn't remove the EXIF data from the photos, which includes the camera's serial number.
Digital DNA could finger Harry Potter leaker - Times Online"The Exif data is like the picture's DNA; you can't switch it off. Every image has it. Some software can be used to strip or edit the information, but you can't edit every field," Mr Solomon said.
A post on the digg.com website claimed that the serial number of the camera which photographed the pages claimed to be from the unpublished Harry Potter, was 560151117.
Canon's head office in Japan confirmed that a serial number would reveal the country in which the camera was sold and possibly also the store, but declined to give any further information about the device used in this case.
The discovery reveals the extent to which people who distribute photographs online can be traced, which is especially relevant given the popularity of social networking sites such as Facebook, which have in some cases been sources of incriminating material.
If traced, the person who photographed the Harry Potter novel could be found guilty of copyright infringement, but would be unlikely to face criminal charges as the photos appear not to have been published for commercial gain, lawyers said.
Thanks to Boing Boing for the link: Boing Boing: Harry Potter photo-leaker might be busted through metadata.
Labels: facebook, metadata, privacy, social networking
Thursday, July 19, 2007
Facebook apps raise additional privacy concerns
In the past few months, Facebook has opened up the Facebook platform to the multitudes who want to write applications for the social networking site. While many are interesting and even more are annoying, all of them raise privacy issues to one degree or another.
Facebook apps don't necessarily follow the Facebook privacy policy:
If you, your friends, or members of your network use any third-party applications developed using the Facebook Platform ("Platform Applications"), those Platform Applications may access and share certain information about you with others in accordance with your privacy settings. You may opt-out of any sharing of certain or all information through Platform Applications on the Privacy Settings page. In addition, third party developers who have created and operate Platform Applications ("Platform Developers"), may also have access to your personal information (excluding your contact information) if you permit Platform Applications to access your data. Before allowing any Platform Developer to make any Platform Application available to you, Facebook requires the Platform Developer to enter into an agreement which, among other things, requires them to respect your privacy settings and strictly limits their collection, use, and storage of your information. However, while we have undertaken contractual and technical steps to restrict possible misuse of such information by such Platform Developers, we of course cannot and do not guarantee that all Platform Developers will abide by such agreements. Please note that Facebook does not screen or approve Platform Developers and cannot control how such Platform Developers use any personal information that they may obtain in connection with Platform Applications. In addition, Platform Developers may require you to sign up to their own terms of service, privacy policies or other policies, which may give them additional rights or impose additional obligations on you, so please make sure to review these terms and policies carefully before using any Platform Application. You can report any suspected misuse of information through the Facebook Platform and we will investigate any such claim and take appropriate action against the Platform Developer up to and including terminating their participation in the Facebook Platform and/or other formal legal action.
I doubt that many people read the privacy policies for each app they load and this is potentially dangerous because of the significant amount of personal information that third parties have access to. Application developers also face some issues that need to be considered.
Take a read of IMPACT®: Third party FaceBook apps are giving rise to serious privacy & legal concerns for a few interesting thoughts on these issues.
Labels: facebook, privacy, social networking
Monday, July 16, 2007
Cell phone info increasingly used as investigative tool
Today's NYT has an article on the amount of information collected by cell phone operators and how it is increasingly being used in police investigations: When the Trill of a Cellphone Brings the Clang of Prison Doors.
Labels: law enforcement, privacy, surveillance
Tuesday, July 10, 2007
Commissioner releases pretexting report
You may recall some time ago when pretexting made the headlines in Canada after a MacLean's reporter purchased the Privacy Commissioner's phone records (Canadian Privacy Law Blog: That's a little cheeky: MacLean's Magazine buys Privacy Commissioner's cellphone records off the 'net). Today the Commissioner released a finding into the incident, accompanied by a big media release:
Data broker exploits human error, weak safeguards to access phone recordsJuly 10, 2007
PIPEDA Case summary #372: Disclosures to data brokers expose weaknesses in telecoms’ safeguards
Here's the release:
Data broker exploits human error, weak safeguards to access phone recordsOTTAWA, July 10 /CNW Telbec/ - Recent experience has shown Canadian companies must take precautions to ensure personal information and customer data is not vulnerable to data thieves and pretexters. Strong identification and authentication procedures are essential in blocking unauthorized attempts to access the personal information of Canadians.
An investigation by the Office of the Privacy Commissioner of Canada (OPC) has found that human error and weaknesses in the policies and procedures of three telecommunications companies allowed a data broker to gain unauthorized access to personal phone records.
The investigation was prompted by an article in Maclean's alleging the magazine had been able to purchase the telephone records of Privacy Commissioner Jennifer Stoddart and a senior Maclean's editor from US-based data broker Locatecell.com.
The investigation found that Locatecell.com used "social engineering" to trick phone company customer service representatives into divulging confidential information, either in the specific instances alleged and/or subsequent test cases. Social engineering involves manipulating people into divulging personal information, for example, by pretexting, or pretending to be someone authorized to obtain the information.
The OPC looked at improper disclosures of personal information to pretexters seeking to gain unauthorized access to phone records of individuals without their knowledge or consent. The three companies investigated were Bell Canada, Telus Mobility and Fido.
"In each case, we found that customer service representatives had not followed the companies' established authentication procedures. We also found that training of customer service representatives was not comprehensive enough to protect customers' personal information from illegal access by pretexters," says Assistant Commissioner Raymond D'Aoust. "As a result, the three companies failed to meet the requirements of the Protection of Personal Information and Electronic Documents Act (PIPEDA)."
All three companies revised their customer authentication procedures shortly after the disclosures took place. The OPC reviewed those changes and recommended further steps to address weaknesses in their policies and procedures to prevent unauthorized individuals from gaining access to customers' personal information. All three companies have since taken additional steps to further mitigate the risks resulting from pretexting and unauthorized access to personal records. The Office of the Privacy Commissioner is generally satisfied that all three companies have put in place an adequate set of measures to address the problems.
Nonetheless, the Assistant Commissioner says the companies should have been better prepared to deal with social engineering in the first place. The issue of data brokers using social engineering to obtain call records in the United States had been in the news some time before these incidents occurred.
"It's particularly troubling that not enough was done to let call centre employees know about this kind of threat," says Assistant Commissioner D'Aoust.
"Given the prevalence of identity theft, it is absolutely crucial that all companies adopt strong authentication processes to help ensure that they are providing information to someone who is actually authorized to have that information. It is equally vital that companies ensure that their employees are following these processes and are aware of the threats to personal information that pretexting poses."
The OPC has developed Guidelines for Identification and Authentication on its web site.
A summary of findings in the three cases is also available on the web site.
New laws in the US have recently made it an offence to use pretexting to obtain individuals' phone records in an effort to curb the activities of US information brokers, including Locatecell.com. However, this does not mean the problem has gone away either in the US, or elsewhere, particularly in other countries, including Canada, where no similar legislation yet exists.
In an appearance before a Parliamentary committee last month, Commissioner Stoddart called on the federal government to work collaboratively with the provinces and international partners to adopt a range of legislative and policy solutions to address this problem.
The Privacy Commissioner of Canada is mandated by Parliament to act as an ombudsman, advocate and guardian of privacy and the protection of personal information rights of Canadians.
Labels: identity theft, pipeda findings, pretexting, privacy
Monday, July 09, 2007
EU US deal extends American Privacy Act to European passengers
Apparently European and American authorities have reached a deal on the transmission of airline passenger information. The deal involves extending US Privacy Act protection to European passengers' data:
U.S. Privacy Act to cover EU citizens - Yahoo! News....Differences over how to balance security needs with concerns over passengers' privacy led to protracted negotiations after a 2004 deal on data sharing was voided by an EU court last year for technical reasons.
Under the new deal, the number of pieces of information transferred to U.S. authorities will be reduced from 34 to 19 — although critics say this is only because some categories of data will be merged.
Data can be kept for a maximum of 15 years. But after the first seven years, data will become "dormant" and can only be accessed on a case-by-case basis under strict rules.
Currently, a maximum of 34 pieces of recorded data — such as passenger names, addresses, seat numbers and credit card and travel details — are transferred to U.S. authorities within 15 minutes of a flight's departure for the United States under Washington's anti-terror screening rules.
The current agreement allows the U.S. Customs and Border Protection agency to disclose so-called Passenger Name Records to other U.S. law enforcement agencies for use in anti-terror investigations if those agencies have data protection standards comparable to the EU's legal demands.
EU governments are to give a final, formal endorsement to the deal later this months after they get the green light from the national parliaments.
Labels: privacy
Google and privacy commentary
Chris Graves, over at Citadel of the Blogs has some interesting things to say about Google and privacy. He's obviously done some thinking about issues such as Google's retention policy, their participation in the Safe Harbor program and cooperation with law enforcement. Take a look: Citadel of the Blogs » Google & Privacy.
Few breaches lead to identity theft, GAO finds
Federal Computer Week recently ran an article on a new report from the GAO that found that few large privacy breaches lead to fraud. The report is here: Personal Information: Data Breaches Are Frequent, but Evidence of Resulting Identity Theft Is Limited; However, the Full Extent Is Unknown (Government Accountability Office); and the FCW.com article is here:
FCW.com News - Few breaches lead to identity theft, GAO findsAlthough data breaches in the public and private sectors are frequent, few incidents of identity theft have occurred as a result of the loss or unauthorized exposure of personal information, the Government Accountability Office said.
Fortunately for potential victims, only three of the 24 biggest breaches that GAO reviewed led to detected incidents of fraud on existing accounts and one incident of the unauthorized creation of a new account, according to GAO’s analysis of available data and interviews with researchers, law enforcement officials and industry representatives.
Retailers and a credit card processor were responsible for the data breaches that led to identity theft. GAO said it uncovered no clear evidence of fraud in 18 incidents, and insufficient data was available to make a determination in two incidents. However, it is difficult to know for certain the magnitude of identity theft, GAO said.
“The extent to which data breaches result in identity theft is not well-known, in large part because it can be difficult to determine the source of the data used to commit identity theft,” wrote David Wood, a director of GAO’s Financial Markets and Community Investment team, in a report posted today.
Perpetrators might hold stolen data for more than a year before using it to commit identity theft, law enforcement officials told GAO.
The data breaches GAO examined represent a fraction of the incidents in which public and private organizations have exposed or lost personal information. From 2005 through 2006, the news media have reported more than 570 data breaches. The House Oversight and Government Reform Committee identified more than 788 data breaches at 17 agencies from January 2003 through July 2006, and banks have reported several hundred incidents to their federal regulators in the past two years.
GAO studied breaches that were reported before July 2005. None involved federal agencies.
Encryption and hardware requirements for access control and certain data-reading equipment can prevent or restrict unauthorized access to data if it falls into the wrong hands.
Requirements to notify affected individuals could serve as incentives for organizations to improve data security practices so they can minimize legal liability and avoid the public relations issues that could result from a publicized breach. But that approach could also result in organizations spending money to develop incident response plans for identifying and notifying affected individuals.
A requirement that is too broad could result in notification of breaches that present little or no risk, perhaps leading consumers to disregard all notices, GAO said.
The agency instead recommended the use of a risk-based notification standard to identify the incidents in which the potential for harm exists and the appropriate actions to take. Consumers who are notified that their data was compromised could then take steps to protect themselves from possible identity theft, such as monitoring their bank or credit card statements for suspicious activity.
“Should Congress choose to enact a federal breach-notification requirement, use of the risk-based approaches that the federal banking regulators and the President’s Identity Theft Task Force advocate could avoid undue burden on organizations and unnecessary and counterproductive notifications to consumers,” Wood wrote in the report.
In April, the task force recommended a national notification standard for public and private organizations similar to its risk-based guidance for federal agencies. It involves notifying consumers who face a significant risk of identity theft, but it avoids excessive notification.
In addition, the Office of Management and Budget has issued guidance to help federal agencies respond to data breaches. No federal law requires that companies or other organizations notify affected individuals of data breaches, although federal banking regulators have provided guidance to the financial institutions they supervise and 36 states have enacted breach-notification laws.
Labels: breach notification, identity theft, privacy
Sunday, July 08, 2007
NY Dept of Ed looks to patch student data system
The New York Post is reporting that the New York Department of Education has issued a tender to "patch leaks" in a massive student database system. See: 'ID LEAK' FEAR IN $80M ED. COMPUTER | By CHUCK BENNETT | New York News | New York City News | NY News.
Labels: privacy
Union raises privacy concerns over Telus' call centre outsourcing
The union representing a portion of Telus' employees is vocally opposing moving call centre jobs to the Philippines. While jobs is the number one concern, they're also making noises about privacy:
TheStar.com - Business - Concern over Telus Manila call centre...The union also said consumers have "reason to be concerned" about who has access to their personal phone records "and who they're talking to when they give out credit card numbers and billing information over the phone."
The company's spokesman responded by saying the concern is unfounded since the records themselves aren't transferred outside of Canada, the Manila agents – as with agents in Canada – access some of the information from secure, encrypted connections and all of the workers in the Philippines are hired with background criminal checks..
"We take the privacy of our customers' information very, very seriously and apply the same training, the same standards in Manila and in Canada. And we comply with Canadian privacy law, regardless of where the service is being provided," Hall said.
Labels: privacy
Privacy Calendar
I've put together a semi-public calendar using Google Calendar called the "Privacy Calendar" to keep track of the various privacy-related events taking place worldwide.
You'll see a summary on the right hand side of the blog.
To make this as useful as possible for everyone who is trying to keep on top of this ever-changing field, please send me any events that I may be missing.
Here are other ways to get the calendar: RSS | iCal | HTML
I hope it is useful to you and I'm always willing to listen to suggestions.
Saturday, July 07, 2007
Oshawa second-hand store bylaw invades privacy
Earlier this week, the Ontario Court of Appeal, in Cash Converters Canada Inc. v. Oshawa (City) (July 4, 2007) (an appeal from Cash Converters Canada Inc. v. Oshawa (City), 2006 CanLII 3469 (ON S.C.)), overturned a City of Oshawa Bylaw that required sellers of second hand goods to collect detailed personal information about those who sell second hand goods to the stores. The bylaw was inconsistent with the Municipal Freedom of Information and Protection of Privacy Act.
Here's what the Toronto Star had to say about it:
TheStar.com - News - Oshawa second-hand store bylaw invades privacy: CourtTracey Tyler
LEGAL AFFAIRS REPORTER
The Ontario Court of Appeal has struck down sections of a controversial Oshawa bylaw that require second-hand dealers to collect detailed personal information from people who sell them goods and transmit the data to police.
The bylaw conflicts with provincial privacy legislation, which requires the collection and retention of personal information to be strictly controlled, the court ruled Wedneday, The 3-0 decision could influence challenges to similar bylaws in other parts of the country, including Alberta and British Columbia.
“This decision comes at a time when cities are gaining broader law-making powers,” said David Sterns, a lawyer representing the Oshawa franchise of Cash Converters Canada Inc., a second-hand store that challenged the bylaw.
“The court has sent a strong signal that all forms of information gathering and surveillance by municipalities are subject to the public’s overriding right to privacy.”
Under the Oshawa bylaw, passed by the city in 2004 as part of a new licensing system for second-hand dealers, stores were required to record the name, address, sex, date of birth, phone number and height of their vendors, who also had to produce three pieces of identification, such as a driver’s licence, birth certificate or passport.
“This information is then transmitted and stored in a police data base and available for use and transmissions by the police without any restriction and without any judicial oversight,” said Justice Kathryn Feldman said, writing on behalf of Associate Chief Justice Dennis O’Connor and Justice Paul Rouleau.
Store owners were required to send reports to police at least daily, in some cases at the time of purchase. The city argued the bylaw was meant to protect consumers from purchasing stolen goods.
But the municipality offered no evidence of a growing problem involving the sale of stolen goods to second-hand dealers, said Feldman.
Nor is there evidence that unscrupulous people are more likely to be deterred by the electronic collection and transmission of personal information, she said.
In 2003, Cash Converters purchased more than 28,000 used items from people in 2003. About 30 of those were seized by police in connection with criminal investigations.
It’s unknown whether any were confirmed as stolen, the court said.
The bylaw did not apply to pawn shops, which are provincially regulated.
See, also, James Daw's column: TheStar.com - columnists - New ruling stands up for privacy.
Labels: alberta, bc, british columbia, law enforcement, ontario, privacy, public sector, retention, surveillance
Thursday, July 05, 2007
Yahoo and Microsoft expected to adjust data retention guidelines
According to the Financial Times, both Yahoo and Microsoft are soon going to announce changes in their privacy polies regarding the retention of search users' information. "Changes" may be stretching it a bit, since neither have publicly come out to say what their retention policies are:
FT.com / Companies / Media & internet - Web search groups to yield on privacyWeb search groups to yield on privacy
By Maija Palmer in London
Published: July 5 2007 22:02 | Last updated: July 5 2007 22:02
Yahoo and Microsoft are preparing to announce concessions in their privacy policies in the next few weeks, as pressure mounts in Europe over the length of time internet search companies should be allowed to hold personal data.
The Article 29 Working Party, a group of national officials that advises the European Union on privacy policy, last month said it wanted to investigate how long companies such as Yahoo and Microsoft keep data on individuals who use their search engines.
The Working Party has already been in discussions with Google over its policies for keeping data, and intends to widen scrutiny to the rest of the market.
The Article 29 group is concerned that data kept by search engine companies can be used to identify individuals and create profiles of their preferences....
Lessons to learn from TJX
David Canton has posted a link to a great article from the McLean Report, which is usually limited to subscribers but he has obtained permission to post it on his site. Check it out: Lessons Learned from TJX: Protect Customer Data at all Costs: eLegal Canton.
MPAA Sets Up Fake Site to Catch Pirates
This is interesting ...
Apparently the MPAA set up a honeypot site called MiiVi.com to catch illegal downloaders and "sharers" of video files. The site is now offline, so I can't get a look at it, but according to a post at Slashdot (Slashdot MPAA Sets Up Fake Site to Catch Pirates), users were encouraged to sign up and download and install a bit of software to manage their downloads. The software actually scoured the users' drives for other copyrighted works and then reported back to the MPAA.
The privacy issues are pretty obvious. I really wanted to take a look at the site's Terms of Use or the software's EULA to see if they at least attempted to get some form of consent for this, but the whole site is dead.
Labels: privacy
10K statements on privacy
I was just browsing Google Inc.'s Form 10-K for 2006 and happend upon this little tidbit under "Risk Factors":
Google Form 10-K for 2006Privacy concerns relating to our technology could damage our reputation and deter current and potential users from using our products and services.
From time to time, concerns have been expressed about whether our products and services compromise the privacy of users and others. Concerns about our practices with regard to the collection, use, disclosure or security of personal information or other privacy-related matters, even if unfounded, could damage our reputation and operating results. While we strive to comply with all applicable data protection laws and regulations, as well as our own posted privacy policies, any failure or perceived failure to comply may result in proceedings or actions against us by government entities or others, which could potentially have an adverse affect on our business.
In addition, as nearly all of our products and services are web based, the amount of data we store for our users on our servers (including personal information) has been increasing. Any systems failure or compromise of our security that results in the release of our users’ data could seriously limit the adoption of our products and services as well as harm our reputation and brand and, therefore, our business. We may also need to expend significant resources to protect against security breaches. The risk that these types of events could seriously harm our business is likely to increase as we expand the number of web based products and services we offer as well as increase the number of countries where we operate.
A large number of legislative proposals pending before the United States Congress, various state legislative bodies and foreign governments concern data protection. In addition, the interpretation and application of data protection laws in Europe and elsewhere are still uncertain and in flux. It is possible that these laws may be interpreted and applied in a manner that is inconsistent with our data practices. If so, in addition to the possibility of fines, this could result in an order requiring that we change our data practices, which could have a material effect on our business. Complying with these various laws could cause us to incur substantial costs or require us to change our business practices in a manner adverse to our business.
Just for fun, I thought I'd check out the 10-K's for Yahoo and DoubleClick.
Yahoo Inc. Form 10-K for 2006Changes in regulations or user concerns regarding privacy and protection of user data could adversely affect our business.
Federal, state, foreign and international laws and regulations may govern the collection, use, retention, sharing and security of data that we receive from our users and partners. In addition, we have and post on our website our own privacy policies and practices concerning the collection, use and disclosure of user data. Any failure, or perceived failure, by us to comply with our posted privacy policies or with any data-related consent orders, Federal Trade Commission requirements or other federal, state or international privacy-related laws and regulations could result in proceedings or actions against us by governmental entities or others, which could potentially have an adverse effect on our business.
Further, failure or perceived failure to comply with our policies or applicable requirements related to the collection, use, sharing or security of personal information or other privacy-related matters could result in a loss of user confidence in us, damage to the Yahoo! brands, and ultimately in a loss of users, partners or advertisers, which could adversely affect our business.
A large number of legislative proposals pending before the United States Congress, various state legislative bodies and foreign governments concern data privacy and retention issues related to our business. It is not possible to predict whether or when such legislation may be adopted. Certain proposals, if adopted, could impose requirements that may result in a decrease in our user registrations and revenues. In addition, the interpretation and application of user data protection laws are in a state of flux. These laws may be interpreted and applied inconsistently from country to country and inconsistently with our current data protection policies and practices. Complying with these varying international requirements could cause us to incur substantial costs or require us to change our business practices in a manner adverse to our business.
Doubleclick Form 10-K for 2006Privacy and Data Protection
We continue to be a leader in promoting consumers’ privacy and understanding the technologies that our clients, marketers, advertising agencies and data companies use to communicate with their existing customers and to acquire new customers. Our Chief Privacy Officer leads our privacy and data protection efforts. Our privacy team focuses on ensuring that we are effectively implementing our privacy policies and procedures and works with our clients to institute and improve their privacy procedures, while helping them to educate their customers about the privacy issues applicable to them. In addition, our privacy team actively participates in a number of industry privacy organizations.
....
Our business may be materially adversely affected by lawsuits related to privacy, data protection and our business practices.
We have been a defendant in several lawsuits and governmental inquiries by the Federal Trade Commission and the attorneys general of several states alleging, among other things, that we unlawfully obtain and use Internet users’ personal information and that our use of ad serving “cookies” violates various laws. Cookies are small pieces of data that are recorded on the computers of Internet users. Although the last of these particular matters was resolved in 2002, we may in the future be subject to additional claims or regulatory inquiries with respect to our business practices. Class action litigation and regulatory inquiries of these types are often expensive and time consuming and their outcome may be uncertain.
Any additional claims or regulatory inquiries, whether successful or not, could require us to devote significant amounts of monetary or human resources to defend ourselves and could harm our reputation. We may need to spend significant amounts on our legal defense, senior management may be required to divert their attention from other portions of our business, new product launches may be deferred or canceled as a result of any proceedings, and we may be required to make changes to our present and planned products or services, any of which could materially and adversely affect our business, financial condition and results of operations. If, as a result of any proceedings, a judgment is rendered or a decree is entered against us, it may materially and adversely affect our business, financial condition and results of operations and harm our reputation.
All three seem relatively boilerplate-ish, but what's interesting is that none of the 10-Ks go to any length to discuss how privacy and customer trust might be a real driver for their brands. Privacy and trust are taken for granted. Some dicussion elsewhere in each document includes privacy as part of their brands, but it is mainly in the context of risks to those brands.
Labels: doubleclick, google, privacy, retention
Wednesday, July 04, 2007
Saskatchewan Commissioner calls for improvements to privacy and access
NEWS RELEASE – July 4, 2007So far, this is the only media coverage I've seen: Prince George Citizen - Commissioner says Sask. officials need to beef up and encourage privacy laws.Saskatchewan Information and Privacy Commissioner tables 2006-2007 Annual Report.
Saskatchewan’s Information and Privacy Commissioner, Mr. Gary Dickson, has submitted his Annual Report for 2006-2007 to the Legislative Assembly. The document is available at the website: www.oipc.sk.ca.
Dickson commented on a number of improvements in terms of compliance by Saskatchewan public bodies with access and privacy requirements. He made recommendations to the Saskatchewan Legislative Assembly as to how the province can do an even better job. This includes:
- An open letter from the Premier to each of his Ministers stressing the importance of compliance with our access and privacy laws.
- Making each Deputy Minister explicitly responsible for ensuring that his or her Department fully complies with our access and privacy laws.
- The need for Ministers, CEOs of Crown corporations and local authorities to provide clear direction and explicit support to the FOIP (access and privacy) Coordinators in each of their organizations.
Commissioner Dickson discussed a worrisome trend in the introduction of new laws and regulations that diminish the information rights of Saskatchewan residents.
Dickson’s report includes 9 proposed steps for the Saskatchewan Government that would promote excellence in meeting access and privacy requirements.
Labels: privacy, saskatchewan
Internet ads under the privacy microscope
The latest developments in internet advertising are getting some pretty close scrutiny. I've posted before about concerns over the proposed Google / DoubleClick merger (see: Google at the bottom of online privacy rankings FTC probes Google / Doubleclick merger, Google is watching you. No surpise, but privacy regulators are ..., Google-DoubleClick deal under privacy fire, Google Buys DoubleClick for $3.1 Billion)
The buzz on this proposed deal continues:
- Google's DoubleClick deal runs into consumer resistance Guardian Unlimited
- European organizations worry about results of GoogleClick deal DM News
- Google-DoubleClick Deal Draws Criticism TIME
And now, not to be outdone, Yahoo! is introducing a new search technology that relies more on the information that the company has collected about users. No surprise that the scheme is receiving a sceptical reception from privacy advocates. See: ABC News: Yahoo's New Ad Program Gets Personal.
Be sure to also read Michael Zimmer's take on this: michaelzimmer.org » Archives » With SmartAds, Yahoo Finally Joins Google…as a Threat to Privacy.
Labels: doubleclick, google, privacy
Tuesday, July 03, 2007
Fears over Facebook identity fraud
The Telegraph online has an interesting article on the tendency of people to let it all hang out on sites such as Facebook. This is not news, but what is interesting is that banks are having to change their identity verification practices because some "security questions" are no longer as secure or as secret as they used to be once your life is being lived online. See: Fears over Facebook identity fraud Uk News News Telegraph.
And a word of caution: don't put your birthdate and your address on your profile. Those two bits of data are often enough to pull your credit report and lead to unfortunate results. And if someone you're dealing with thinks your mother's maiden name leads to security, walk away.
Labels: facebook, privacy, social networking
Sunday, July 01, 2007
Respectful surveillance?
Last week, Bruce Schneier linked to an article on "respectful cameras" that can recognize faces and obscure them with an oval. The oval can be removed in the event of an investigation. See: Schneier on Security: Surveillance Cameras that Obscure Faces. But one commentator says it's just the "illusion of privacy".
Labels: privacy, schneier, surveillance
OPC finds LSAT fingerprinting violates PIPEDA
In a preliminary letter to the complainant, the Office of the Privacy Commissioner of Canada has concluded that the Law School Admissions Council violates PIPEDA by requiring candidates to submit to fingerprinting at the time the LSAT test is taken:
CIPPIC News « CIPPICIn a decision released earlier this month, the Privacy Commissioner of Canada found that the requirement for Canadian students to provide a finger/thumb print in order to take the Law School Admission Test (LSAT) is an unnecessary infringement of privacy.
One of the most interesting aspects of the letter is the conclusion that the non-profit LSAC is engaged in commercial activities sufficient to have PIPEDA apply in the first place.
Also, the Assistant Commissioner's conclusion turned on the four point test applied in the past to video surveillance:
- Is the measure demonstrably necessary to meet a specific need?
- Is it likely to be effective in meeting that need?
- Is the loss of privacy proportional to the benefit gained?
- Is there a less privacy-invasive way of achieving the same end?
Labels: biometrics, patriot act, privacy, surveillance, video surveillance
Wired seeking worst corporate privacy offenders
Labels: privacy
![]()

The Canadian Privacy Law Blog is licensed under a
Creative Commons Attribution-Noncommercial-No Derivative Works 2.5 Canada License.




