The Canadian Privacy Law Blog: Developments in privacy law and writings of a Canadian privacy lawyer, containing information related to the Personal Information Protection and Electronic Documents Act (aka PIPEDA) and other Canadian and international laws.
Recent Posts
- This blog has moved
- Some thoughts on street photography
- RCMP changes rules for criminal records checks
- Saskatchewan amends privacy regs to permit solicia...
- US Federal judge declares warrantless wiretapping ...
- Commisser releases discussion paper on cloud compu...
- Heathrow worker given police warning for body scan...
- How Privacy Vanishes Online, a Bit at a Time
- Facebook plans to allow users to "share" location
- Drawing the curtain on ISP cooperation with law en...
On Twitter
About this page and the author
 The author of this blog,
David T.S. Fraser, is a Canadian privacy lawyer who practices with the
firm of McInnes Cooper. He is the author of the Physicians' Privacy Manual. He has a national and international practice advising corporations and individuals on matters related to Canadian privacy laws.
The author of this blog,
David T.S. Fraser, is a Canadian privacy lawyer who practices with the
firm of McInnes Cooper. He is the author of the Physicians' Privacy Manual. He has a national and international practice advising corporations and individuals on matters related to Canadian privacy laws.
For full contact information and a brief bio, please see David's profile.
Please note that I am only able to provide legal advice to clients. I am not able to provide free legal advice. Any unsolicited information sent to David Fraser cannot be considered to be solicitor-client privileged.
Privacy Calendar
Archives
- January 2004
- February 2004
- March 2004
- April 2004
- May 2004
- June 2004
- July 2004
- August 2004
- September 2004
- October 2004
- November 2004
- December 2004
- January 2005
- February 2005
- March 2005
- April 2005
- May 2005
- June 2005
- July 2005
- August 2005
- September 2005
- October 2005
- November 2005
- December 2005
- January 2006
- February 2006
- March 2006
- April 2006
- May 2006
- June 2006
- July 2006
- August 2006
- September 2006
- October 2006
- November 2006
- December 2006
- January 2007
- February 2007
- March 2007
- April 2007
- May 2007
- June 2007
- July 2007
- August 2007
- September 2007
- October 2007
- November 2007
- December 2007
- January 2008
- February 2008
- March 2008
- April 2008
- May 2008
- June 2008
- July 2008
- August 2008
- September 2008
- October 2008
- November 2008
- December 2008
- January 2009
- February 2009
- March 2009
- April 2009
- May 2009
- June 2009
- July 2009
- August 2009
- September 2009
- October 2009
- November 2009
- December 2009
- January 2010
- February 2010
- March 2010
- April 2010
Links


Blogs I Follow
Small Print
The views expressed herein are solely the author's and should not be attributed to his employer or clients. Any postings on legal issues are provided as a public service, and do not constitute solicitation or provision of legal advice. The author makes no claims, promises or guarantees about the accuracy, completeness, or adequacy of the information contained herein or linked to. Nothing herein should be used as a substitute for the advice of competent counsel.
This web site is presented for informational purposes only. These materials do not constitute legal advice and do not create a solicitor-client relationship between you and David T.S. Fraser. If you are seeking specific advice related to Canadian privacy law or PIPEDA, contact the author, David T.S. Fraser.
Wednesday, December 05, 2007
Credit-card company facing liquidation
I am surprised this hasn't received more coverage. Cardsystems is facing bankruptcy as a result of the very high profile data breach in 2005. See: Credit-card company facing liquidation | www.azstarnet.com ®.
Labels: cardsystems, privacy
Wednesday, September 26, 2007
Inadequate security safeguards led to TJX breach, Commissioners say
The federal Privacy Commissioner and the Information and Privacy Commissioner of Canada have released their reports on the TJX/Winners breach (Report of Findings (September 25, 2007) Privacy Commissioner of Canada and Investigation Report P2007-IR-006). The moral of the story: don't collect information you don't need, don't keep it any longer than you need and properly secure the information you have.
Here's the media release:
News Release: Inadequate security safeguards led to TJX breach, Commissioners say (September 25, 2007) - Privacy Commissioner of CanadaInadequate security safeguards led to TJX breach, Commissioners say
September 25, 2007 –The risk of a breach of sensitive personal information held by TJX Companies Inc., the US parent company of Winners and HomeSense stores in Canada, was foreseeable, but the company failed to put in place adequate security safeguards, an investigation by the Privacy Commissioners of Canada and Alberta has found.
“The company collected too much personal information, kept it too long and relied on weak encryption technology to protect it – putting the privacy of millions of its customers at risk,” says Privacy Commissioner of Canada Jennifer Stoddart.
“Criminal groups actively target credit card numbers and other personal information,” says Commissioner Stoddart. “A database of millions of credit card numbers is a potential goldmine for fraudsters and it needs to be protected with solid security measures.
“The TJX breach is a dramatic example of how keeping large amounts of sensitive information – particularly information that is not required for business purposes – for a long time can be a serious liability.”
The joint investigation by the two Commissioners was launched after TJX disclosed in January that its computer system had been breached. This breach involved millions of credit and debit card numbers as well as other personal information, such as driver’s license numbers collected when customers returned merchandise without receipts.
“This case is a wake-up call for all retailers. They must collect only the personal information necessary for a transaction,” says Frank Work, the Information and Privacy Commissioner of Alberta.
“One positive outcome of this extremely unfortunate breach is that TJX worked cooperatively with us to develop a new process for dealing with unreceipted returns which strikes an appropriate balance between privacy rights and a retailer’s need to take steps to prevent fraud.”
TJX believes the intruder may have initially gained to customer information via the wireless local area networks at two of its US stores. Customer information was stolen from mid-2005 through December 2006, a TJX investigation found. Some stolen information involved transactions dating back to 2002.
Stolen information included credit card account data as well as data collected when customers returned merchandise without a receipt (drivers’ license numbers, names and addresses).
The investigation concluded TJX did not comply with the federal private sector privacy law, the Personal Information Protection and Electronic Documents Act (PIPEDA), and Alberta’s Personal Information Protection Act (PIPA). The investigation found:
- TJX did not properly manage the risk of an intrusion against the amount of customer data that it collected.
- The company failed to act quickly in converting from a weak encryption standard to a stronger standard. The conversion process took two years to complete, during which time the breach occurred.
- TJX did not meet its duty to monitor its computer systems vigorously. An adequate monitoring system should have alerted the company of an intrusion prior to December 2006.
- The company did not adhere to the requirements of the Payment Card Industry Data Security Standard, which was developed to address the growing problem of credit card data theft.
The investigation also found the company did not have a reasonable purpose to collect driver’s license and other identification numbers when unreceipted merchandise was returned. TJX stated it asked for this information as part of a fraud prevention process to identify people frequently returning merchandise. It retained the driver’s license numbers – an extremely valuable piece of information for identity thieves – indefinitely.
In response to these concerns, TJX proposed a new process to address fraudulent returns. Store staff will continue to ask for identification, however, information such as a driver’s license number will instantly be converted into a unique identifying number when it is keyed into the point-of-sale system. This will allow the company to track unreceipted merchandise returns without keeping original driver’s license numbers in its system.
The Commissioners called on TJX to take a number of steps to improve its security measures and privacy practices and are pleased the company has agreed to follow these recommendations.
Commissioner Stoddart says the Winners/HomeSense breach illustrates the need to get security right in the first place to avoid the potentially huge costs of mopping up after a security breach. “Organizations need to ensure they have multiple layers of security and that they keep up with advances in security technologies. The cost of failing to do this can be enormous – not only to a company, but to its customers,” she says, adding that a data breach can also have a major impact on credit card companies, banks, law enforcement agencies and regulatory bodies.
A summary of the findings in the case is available on the Commissioners’ websites.
The Privacy Commissioner of Canada is mandated by Parliament to act as an ombudsman, advocate and guardian of privacy and the protection of personal information rights of Canadians.
The Information and Privacy Commissioner of Alberta has a mandate to promote a society where personal privacy is respected and public bodies are open and accountable.
Saturday, May 12, 2007
Canada's No-fly list takes to the skies
Canada's new no-fly list is ready to take off:
CNW GroupAir security strengthened - Passenger Protect ready to take flight
OTTAWA, May 11 /CNW Telbec/ - The Honourable Lawrence Cannon, Minister of Transport, Infrastructure and Communities, together with the Honourable Stockwell Day, Minister of Public Safety, today announced new regulations that will strengthen air passenger security screening. Once implemented, new measures under a program known as Passenger Protect will prevent persons who pose an immediate threat to aviation security from boarding a commercial aircraft.
This made-in-Canada program was developed to provide an additional layer of security for the aviation system and to enhance public safety in a way that complies with the Canadian Charter of Rights and Freedoms and federal privacy legislation.
"Canadians want to fly secure, and Passenger Protect is a significant step forward. We must remember that Canada is not immune to the threat of terrorism and we must remain vigilant," said Minister Cannon. "Passenger Protect will not only make Canada's aviation system more secure, it will also help keep the world's skies safe by reaching beyond Canadian borders to screen everyone getting on a flight to Canada."
Under the new program, the Government of Canada is maintaining a list of specified persons who may pose an immediate threat to aviation security should they attempt to board a flight. Air carriers will be able to screen passengers against the specified persons list through a secure online system. If the air carrier identifies a person as a possible match with an entry on the list, the air carrier will contact Transport Canada to confirm the passenger's identity, and obtain a decision whether or not to allow him or her to board the flight. "Canada has one of the best aviation systems in the world and is always looking for ways to increase the safety and security of the travelling public,"said Minister Day.
The Government of Canada has held discussions with airlines, airports, and labour representatives, as well as civil liberties and ethno-cultural groups in developing Passenger Protect, to create a program that enhances security, respects the needs and realities of the aviation industry and protects the rights of Canadians. As part of the consultations, Transport Canada has established a reconsideration process to provide a non-judicial, efficient way for any members of the public who have been denied boarding to have their cases reviewed by persons independent of those who made the original recommendation.
Transport Canada has worked closely with the Office of the Privacy Commissioner in order to further strengthen the privacy provisions of the program. Implementation for flights within Canada and international flights to and from Canada will begin on June 18, 2007.
As of this date, new Identity Screening Regulations will require air passengers within Canada who appear to be 12 years of age or older to present one piece of government-issued photo identification (ID) that shows name, date of birth and gender or two pieces of government-issued ID - one of which shows name, date of birth and gender - before boarding an aircraft. The boarding pass provided by the air carrier must match the name on the ID.
Canadians will not need a passport for travel within Canada but rather can present a range of government-issued ID to the air carriers including a health card, a birth certificate, a driver's licence and a social insurance card. Current requirements for international travel will remain in place. This practice is consistent with procedures currently in use by most major airlines, and will allow the air carrier and Transport Canada to confirm the identity of a passenger who is a possible match with an entry on the specified persons list.
These proposed regulations were first published in the Canada Gazette, Part I on October 28, 2006, after which a 75-day period followed to enable interested parties and the public to provide comments.
The final regulations will be published in the Canada Gazette, Part II on May 16, 2007.
A backgrounder with more information on the Passenger Protect program and the new Identity Screening Regulations is attached.
<< -------------------------------------------------------------------------
BACKGROUNDER
-------------------------------------------------------------------------
PASSENGER PROTECT PROGRAM
-------------------------
The Government of Canada began consulting with industry on passenger assessment in May 2004, and expanded consultations on a program proposal for Passenger Protect in the summer of 2005. Consultations with air carriers, airports, labour representatives, civil liberties and ethno-cultural groups as well as the Office of the Privacy Commissioner were essential to the successful design and implementation of a program that enhances security, respects the needs and realities of the aviation industry, and ensures that the privacy and human rights of Canadians are protected.
The Passenger Protect program adds another layer of security to Canada's aviation system to help address potential threats. Terrorist groups continue to target civil aviation, and seek means to defeat existing safeguards and measures.
Under the program, the Government of Canada is maintaining a list with the name, date of birth and gender of each specified person that will be provided to airlines in secure form. The airlines will compare the names of individuals intending to board flights with the names on the specified persons list, and will verify with the individual's government-issued identification when there is a name match. Identification will be verified in person at the airport check-in counter. When the airline verifies that an individual matches in name, date of birth and gender with someone on the list, the airline will be required to inform Transport Canada.
A Transport Canada officer will be on duty 24 hours a day, every day, to receive calls from airlines when they have a potential match with a specified person on the list. Transport Canada will verify information with the airline, confirm whether the individual poses an immediate threat to aviation security and inform the airline, if required, that the individual is not permitted to board the flight. The Royal Canadian Mounted Police (RCMP) would be notified immediately in the event of a match, and police of jurisdiction at the airport would be informed and take action as required.
The Passenger Protect program will be implemented for Canadian domestic flights and international flights to and from Canada on June 18, 2007. Creating the Specified Persons List
The Minister of Transport, Infrastructure and Communities has the authority under the Aeronautics Act, to specify an individual who is a threat to aviation security and to require airlines to provide information about the specified person.
A Transport Canada-led Advisory Group will assess individuals on a case-by-case basis using information provided by the Canadian Security Intelligence Service and the RCMP, and will make recommendations to the Minister of Transport, Infrastructure and Communities concerning their designation as specified persons or the removal of that designation. The Advisory Group includes a senior officer from the Canadian Security Intelligence Service and a senior officer from the RCMP (as advised by the Department of Justice), with input from representatives from other Canadian government departments and agencies.
Individuals are added to the specified persons list based on their actions, which lead to a determination that they may pose an immediate threat to aviation security, should they attempt to board an aircraft. Guidelines in making that determination are focused on aviation security, and may include:
- an individual who is or has been involved in a terrorist group, and who, it can reasonably be suspected, will endanger the security of any aircraft or aerodrome or the safety of the public, passengers or crew members;
- an individual who has been convicted of one or more serious and life-threatening crimes against aviation security; and
- an individual who has been convicted of one or more serious and life-threatening offences and who may attack or harm an air carrier, passengers or crew members.
Identity Screening Regulations
As of June 18th 2007, new Identity Screening Regulations will require airlines to screen each person's name against the specified persons list before issuing a boarding pass, for any person who appears to be 12 years of age or older. The regulations take into account the various ways in which the boarding pass may be obtained: at a kiosk, through the Internet, or at an airport check-in counter.
Where there is check-in via Internet or kiosks, airlines will not allow printing of the boarding pass when there is a name match with the specified persons list. Passengers refused a boarding pass at a kiosk or through the Internet will be directed to the airline agent for in-person verification of government-issued identification (ID). ID verification will determine whether the name, date of birth and gender match those of a listed person.
The regulations also require air carriers to screen individuals at the boarding gate by comparing the name on government-issued ID with the name on the boarding pass. If the name on the ID is not the same as the name on the boarding pass, the air carrier will be required to check the name on the ID against the list.
Transport Canada will work with air carriers to provide training for agents and staff who will be involved in implementing the ID verification requirement, and establish procedures that respect the rights of passengers.
The ID requirement under the Passenger Protect program is for one piece of valid government-issued photo ID that shows name, date of birth and gender, such as a driver's licence or a passport, or two pieces of valid government-issued ID, at least one of which shows name, date of birth and gender, such as a birth certificate. The verification of passengers' ID is already a practice followed by most major air carriers in Canada.
The regulations will be published in the Canada Gazette, Part II on May 16, 2007.
Reconsideration and Appeals
The Passenger Protect program also includes a reconsideration process for individuals who wish to contest the denial of boarding. An individual who has been denied boarding under the Passenger Protect program will be able to apply to Transport Canada's Office of Reconsideration (OOR), which may arrange for an independent assessment of the case and make a recommendation. The goal is to provide a non-judicial, efficient mechanism for any member of the public to have their case reviewed by persons independent of those who made the original recommendation to the Minister. Individuals have the further option of making application to Federal Court for judicial review. Privacy and Human Rights
The protection of privacy and human rights is a core element of the Passenger Protect program. In developing the program, Transport Canada worked with stakeholders and consulted with civil liberties and ethno-cultural groups, and the Office of the Privacy Commissioner on privacy aspects.
A summary of the Privacy Impact Assessment conducted on the Passenger Protect program is available on the Transport Canada website at www.tc.gc.ca/vigilance/sep/passenger_protect/executive_summary/menu.htm. In addition, the Office of the Privacy Commissioner of Canada posed a series of questions to Transport Canada about the Passenger Protect program in August 2005. The questions and the answers shed light on the privacy protection features of the program and are available on the Web at www.tc.gc.ca/vigilance/sep/passenger_protect/Q&A/menu.htm.
More details on the Passenger Protect program and the new Identity Screening Regulations are available on Transport Canada's website at www.tc.gc.ca/vigilance/sep/passenger_protect/menu.htm.
May 2007
Labels: air travel, airlines, cardsystems, health information, international travel, national security, no-fly list, privacy
Monday, May 07, 2007
WSJ sheds light on TJX breach methods
David Canton has just posted a link to a very interesting and insightful article on the TJX/Winners breach, which sheds light on how the scammers were able to penetrate the TJX system to take approximately TWO HUNDRED MILLION credit card numbers.
How Credit-Card Data Went Out Wireless Door - WSJ.com... When wireless data networks exploded in popularity starting around 2000, the data was largely shielded by a flawed encoding system called Wired Equivalent Privacy, or WEP, that was quickly pierced. The danger became evident as soon as 2001, when security experts issued warnings that they were able to crack the encryption systems of several major retailers.
By 2003, the wireless industry was offering a more secure system called Wi-Fi Protected Access or WPA, with more complex encryption. Many merchants beefed up their security, but others including TJX were slower to make the change. An auditor later found the company also failed to install firewalls and data encryption on many of its computers using the wireless network, and didn't properly install another layer of security software it had bought. The company declined to comment on its security measures.
The hackers in Minnesota took advantage starting in July 2005. Though their identities aren't known, their operation has the hallmarks of gangs made up of Romanian hackers and members of Russian organized crime groups that also are suspected in at least two other U.S. cases over the past two years, security experts say. Investigators say these gangs are known for scoping out the least secure targets and being methodical in their intrusions, in contrast with hacker groups known in the trade as "Bonnie and Clydes" who often enter and exit quickly and clumsily, sometimes strewing clues behind them.
The TJX hackers did leave some electronic footprints that show most of their break-ins were done during peak sales periods to capture lots of data, according to investigators. They first tapped into data transmitted by hand-held equipment that stores use to communicate price markdowns and to manage inventory. "It was as easy as breaking into a house through a side window that was wide open," according to one person familiar with TJX's internal probe. The devices communicate with computers in store cash registers as well as routers that transmit certain housekeeping data.
After they used that data to crack the encryption code the hackers digitally eavesdropped on employees logging into TJX's central database in Framingham and stole one or more user names and passwords, investigators believe. With that information, they set up their own accounts in the TJX system and collected transaction data including credit-card numbers into about 100 large files for their own access. They were able to go into the TJX system remotely from any computer on the Internet, probers say....
Labels: cardsystems, privacy, retail, security, tjx
Thursday, March 01, 2007
This time it's personal
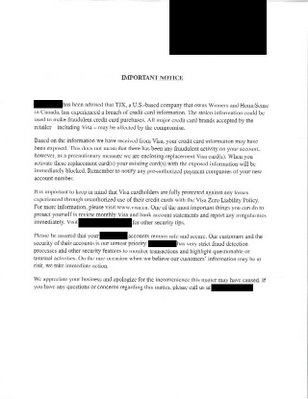
In addition to my weekly New Yorker magazine, today's mail contained a plain envelope with a PO Box return address. From a mile away, I could tell it was a credit card. Like many people recently, my bank has sent me a new credit card in the mail because I shopped at Winners. According to the letter, there is reason to believe my credit card was compromised in the Winners/TJX breach. The form letter tells me that there's been no evidence of fraudulent activity, but this is just in case.
When the TJX story broke, I attempted to contact their privacy officer through the address on the website. What I was looking for was a fax number becuase I did not want to communicate with them, particularly about my credit card, via e-mail. That was months ago and no contact and no reply. Not impressive.
I just went to the Winners website and tried to check out their IMPORTANT CUSTOMER ALERT, which connects (or rather doesn't connect) to a TJX server:
Less impressive.
Going directly to the TJX website provided a working link:
As TJX’s President and Chief Executive Officer, I want our customers to know how much I personally regret any difficulties you may experience as a result of the unauthorized intrusion into our computer systems. We are working with leading computer security firms to investigate the problem and enhance our computer security in order to protect our customers’ data. We are dedicating significant resources to evaluate the issue. Given the nature of the breach, the size and international scope of our operations and the complexity of the way credit card transactions are processed, the evaluation is, by necessity, taking time.Since we learned of the probability of a breach in mid-December 2006, we have cooperated with law enforcement as well as with the banks and credit card companies that process our customer transactions. Further, we have established customer helplines in three countries and are making available a great deal of helpful information on our company websites.
We are committed to continue to address the situation and to provide periodic updates as we learn more. We have reported updated information in a press release which you will find below.
Additionally, I encourage you to access the information we are providing on this website to learn more about steps you can take to protect your credit and debit card information, or to contact our special customer helplines.
With the help of computer security experts, we have strengthened the security of our computer systems and we believe customers should feel safe shopping in our stores. We value the trust our customers place in us and again, I’d like you to know that we sincerely apologize for any difficulties you may be caused. Thank you for continuing to shop at our stores and for your years of loyal patronage.
Respectfully,
Carol Meyrowitz
President and Chief Executive Officer
Those affected may seek some perverse comfort that TJX may face significant penalties under the PCI Data Security Standard.
It will be interesting (but certainly not remedial in any way) to see what the Privacy Commissioner concludes about this investigation.
Labels: cardsystems, privacy, tjx
Wednesday, February 21, 2007
T.J. Maxx probe finds broader hacking
This isn't good:
T.J. Maxx probe finds broader hacking | Tech News on ZDNetThe TJX Companies, the discount retailer best known for its T.J. Maxx and Marshalls clothing stores, said Wednesday that its hacking investigation has uncovered more extensive exposure of credit and debit card data than it previously believed.
Information on millions of TJX customers may have been exposed in the long-running attack, which was made public last month. It affects customers of any of TJX store in the U.S., Canada or Puerto Rico, with the exception of its Bob's Stores chain.
The breach of credit and debit card data was initially thought to have lasted from May 2006 to January. However, TJX said Wednesday that it now believes those computer systems were first compromised in July 2005.
TJX said credit and debit card data from January 2003 through June 2004 was compromised. The company previously said that only 2003 data may have been accessed. According to TJX, however, some of the card information from September 2003 through June 2004 was masked at the time of the transactions.
The company added that names and addresses apparently were not included with the card information, that debit card PIN numbers are not believed to have been vulnerable, and that data from transactions made with debit cards issued by Canadian banks likely were not vulnerable.
TJX also found that there was evidence of intrusion into the system that handles customer transactions for its T.K. Maxx stores in the United Kingdom and Ireland, but that there has been no confirmation that anyone actually accessed that data.
In addition to these exposures, TJX said there were more breaches of driver's license information than it previously thought. These included the license numbers, names and addresses of customers making merchandise returns in the U.S. and Puerto Rico locations of T.J. Maxx, Marshalls and HomeGoods stores. That compromised data, according to TJX, is restricted to returns without receipts that took place in the last four months of 2003, as well as in May 2004 and June 2004.
TJX plans to notify customers whose driver's license data may have been accessed.
The company, which is continuing its investigation, encourages customers to check their credit-card and bank-account records and look for further updates on its website.
Labels: cardsystems, privacy, retail, tjx
Saturday, January 27, 2007
Incident: Club Monaco associated with privacy breach
Fashion retailer Club Monaco is now associated with a third information breach, though the details are very sketchy. From the Globe & Mail:
globeandmail.com : globeinvestor.com : Clothing chain tipped to security breach:Fashion retailer Club Monaco has called in the RCMP to investigate a possible privacy breach involving customers' credit card numbers -- the third time in the past week that a major Canadian company has been plagued by security issues.
Club Monaco confirmed it was alerted to the problem by a credit card processor late last year and said it immediately hired a forensic firm to help the Mounties with their probe. Banks and other card issuers were also notified of the problem, and have been combing client records for any signs of fraud, according to sources in the financial community.
Investigators have found no evidence to suggest a breach occurred, a spokeswoman for the clothing chain said yesterday, adding that the data under investigation do not include names, addresses or phone numbers. She said the company has not determined how many customers might be affected.
'We've been told through the report thus far that our systems are very secure,' Wendy Smith said. 'It's an active investigation.'...
Labels: cardsystems, incident, privacy
Thursday, January 18, 2007
Incidents: Rash of info breaches with Canadian connections
This has been a crazy week for privacy breaches in Canada and the week isn't over yet. I can't recall the last time I had so many media inquiries.
In addition to those below, I've been asked about two other incidents that will likely break in the next few days. (Since I heard about them from journalists, it would be rude to scoop them on the blog.)
Today we've heard of a significant announcement made by Talvest Mutual Funds
Talvest Mutual Funds issues statement regarding missing back up computer fileMONTREAL, Jan. 18 /CNW/ - Talvest Mutual Funds today announced that a backup computer file containing client information has recently gone missing while in transit between its offices.
The backup file contained information relating to the process used to open and administer approximately 470,000 current and former Talvest client accounts and may have included client names, addresses, signatures, date of birth, bank account numbers, beneficiary information and / or Social Insurance Numbers. Talvest has retained original copies of their files on its secure website.
While Talvest has no evidence to suggest this backup file has been inappropriately accessed, the manager of Talvest Mutual Funds, CIBC Asset Management, has taken precautionary measures to protect its clients. These actions include:
- Notifying all affected clients by letter.
- Compensating any affected Talvest clients for monetary loss that arises directly from unauthorized access of personal information contained on this file.
- Providing affected Talvest clients the opportunity to enrol in a credit monitoring service at no cost. This service will provide added security on client credit files at major Credit Reporting agencies.
- Establishing a dedicated call centre and website to deal with any affected Talvest client inquiries.
- Advising affected Talvest clients to regularly review activity on all their financial accounts and report any unauthorized activity immediately to their financial institution.
- Working with the police to investigate this incident and retrieve this backup file.
"We are in the process of contacting affected Talvest clients by letter to advise them of this issue and to detail the steps we are taking to safeguard their information," said Steve Geist, President of CIBC Asset Management. "Although, we have no evidence that the information contained in the backup file has been accessed in any way, we are acting out of an abundance of caution and want to assure our clients that we are taking all steps possible to address this matter. Any issue that causes disruption to our clients is of great concern to us and we regret the inconvenience this may cause our Talvest Mutual Fund Clients."
For more information on this matter, Talvest Mutual Fund clients are advised to visit www.talvest.com.
And with a report from the CBC:
CIBC loses data on 470,000 Talvest fund customersCIBC Asset Management says a backup computer file containing information on almost half a million of its Talvest Mutual Funds clients has gone missing.
The company says the missing data was in a file that disappeared "while in transit between our offices." The file had personal and financial details on current and former clients of Talvest Mutual Funds, which is a CIBC subsidiary.
The information may have included client names, addresses, signatures, dates of birth, bank account numbers, beneficiary information and/or Social Insurance Numbers.
Talvest says there's no indication that the missing backup file has been "inappropriately accessed," but says CIBC will be taking a number of precautions.
"We are in the process of contacting affected Talvest clients by letter to advise them of this issue and to detail the steps we are taking to safeguard their information," said Steve Geist, president of CIBC Asset Management.
Computer fraud expert Thomas Keenan from the University of Calgary said there's good reason for the company to alert their customers. "Because what's on there [the missing file] is everything you need to know to do identity theft," he told CBC News.
The privacy commissioner of Canada, Jennifer Stoddart, announced that she is launching an investigation.
"Although I appreciate that the bank notified us of this incident and that it is working co-operatively with my office, I am nevertheless deeply troubled, especially given the magnitude of this breach, which puts at risk the personal information of hundreds of thousands of Canadians," Stoddart said in a statement.
Talvest has set up special phone lines for clients who want more information.
The report follows news of a potential corporate privacy breach that could affect as many as two million Visa credit card holders in Canada.
The owner of Winners and HomeSense stores warned Thursday that hackers gained access to its computer system and credit card numbers may have been improperly accessed.
Also, a breach involving TJX, the parent of TJ Maxx, Winners and Homesense, may have exposed the personal information of Canadian customers of that store:
globeandmail.com: Computer breach exposes TJX shoppers to fraudSECURITY
Parent of Winners, HomeSense targeted
MARINA STRAUSS AND SINCLAIR STEWART
Tens of millions of credit card customers in Canada and the United States may have been exposed to fraud during a computer security breach at discount retailer TJX Cos., the U.S. parent of Winners and HomeSense.
TJX, which also owns T. J. Maxx and Marshalls, said yesterday it discovered the "unauthorized intrusion" in mid-December and has been working with police and security experts on both sides of the border to investigate the incident and tighten security procedures.
The retailer declined to say exactly how many customers are affected. But sources close to Visa said the company notified banks and other issuers last week that approximately 20 million of its cards around the world may have been involved. Some in the financial industry estimate the number in Canada could be as high as two million. It's not clear how many customers of other credit card companies have been left vulnerable.
The problem was tied to the computer systems that process and store information about customer transactions involving credit cards, debit cards, cheques and merchandise returns -- some of them going back to 2003. The Royal Canadian Mounted Police and the U.S. Secret Service have been called in to investigate.
"While TJX has specifically identified some customer information that has been stolen from its systems, the full extent of the theft and affected customers is not yet known," the Framingham, Mass-based retailer said in a statement.
...
"I was stunned," said retail analyst John Chamberlain at Canadian Bond Rating Service. "That's not what you expect from a big retailer. You really expect that they would have stronger systems than that. You get to the point that you trust a retailer to keep that information."
Customers consider the shopping at TJX stores as a "treasure hunt," never quite sure what they'll find, he said. As a result, customers probably use plastic there more often because they don't always know how much they'll spend, he said.
Company officials didn't return calls. Their statement said the retailer kept the matter secret until yesterday at the request of law enforcement. The company said it promptly notified credit card companies and firms that process customer transactions.
An intruder grabbed information dealing with credit and debit cards sales in TJX stores during 2003 and part of 2006, according to the company. However, a source said that the debit transactions were confined to the U.S. market. TJX has been able to identify "a limited number" of credit card and debit card holders whose information was taken.
Canadian banks are scrambling to assess the potential damage. Tania Freedman, a Visa spokeswoman, said the company is forwarding information to banks. "These accounts were potentially exposed, [but] not all accounts that are exposed will experience fraud," she said, adding that customers are protected by the card's zero-liability policy.
...
In Canada, TJX runs 184 Winners and 68 HomeSense stores.
Expect much more info to come.....
Update (20070118): The Privacy Commissioner of Canada has inititated a complaint on her own accord related to the Talvest breach: Privacy Commissioner launches investigation of CIBC breach of Talvest customers' personal information.
Labels: cardsystems, identity theft, incident, privacy, retail, tjx
Wednesday, October 18, 2006
Ontario Commissioner unveils plan for privacy-embedded Internet identity
As alluded to earlier this week, the Information and Privacy Commissioner of Ontario has released her whitepaper, 7 Laws of Identity: The Case for Privacy-Embedded Laws of Identity in the Digital Age. It's interesting reading but probably will not be comprehensible to lay readers. Here's the media release and links for more info:
IPC - Commissioner Ann Cavoukian unveils plan for privacy-embedded Internet identityTORONTO – Consumers today are being spammed, phished, pharmed, hacked and otherwise defrauded out of their personal information in alarming numbers, in large part because there are few reliable ways for them to distinguish the “good guys” from the “bad” online.
Dr. Ann Cavoukian, Information and Privacy Commissioner of Ontario, today announced her support for a global online identity system framework by outlining seven far-reaching “privacy-embedded” laws, which would help consumers verify the identity of legitimate organizations before making online transactions.
These laws were inspired by the 7 Laws of Identity formulated through a global dialogue among security and privacy experts, headed by Kim Cameron, Chief Identity Architect at Microsoft. The 7 Laws of Identity propose the creation of a revolutionary “identity layer” for the Internet, providing a broad conceptual framework for a universal, interoperable identity system.
Dr. Cavoukian’s 7 Laws of Identity: The Case for Privacy-Embedded Laws of Identity in the Digital Age incorporates additional key insights from the privacy arena. An extension of the original 7 Laws, they encourage privacy-enhanced features to be embedded into the design of the IT architecture and be made available early in the emerging universal identity system.
The Internet was built without a way to know who and what individuals are connecting to. This limits what people can do and exposes computer users to potential fraud. If the IT industry and government do nothing, the result will be rapidly proliferating episodes of theft and deception that will cumulatively erode public trust. That confidence is already eroding as a result of spam, phishing and identity theft, which leaves online consumers vulnerable to the misuse of their personal information and minimizes the future potential of e-commerce. The Privacy-Embedded Laws of Identity support the global initiative to empower consumers to manage their own digital identities and personal information in a much more secure, verifiable and private manner.
“Just as the Internet saw explosive growth as it sprang from the connection of different proprietary networks, an ‘Identity Big Bang’ is expected to happen once an open, non-proprietary and universal method to connect identity systems and ensure user privacy is developed in accordance with privacy principles,” said Dr. Cavoukian. “Microsoft started a global privacy momentum. Already, there is a long and growing list of companies and individuals who now endorse the7 Laws of Identity and are working towards developing identity systems that conform to them.”
“We are honoured to work with Dr. Cavoukian on this project, who along with us and other IT companies are endorsing global privacy laws and fair information practices,” said Peter Cullen, Chief Privacy Strategist, Microsoft. “Best business practices that ensure both security and identity are what is needed to help keep the Internet’s integrity intact. These 7 Laws, with specific articulation of privacy protections, are a big step in that direction.”
Other privacy-enhanced laws will help to minimize the risk that one’s online identities and activities will be linked together, said Dr. Cavoukian. “We already expect this in the real world when we present a library card, for example, to check out a book, and present our passport to cross a national border. We don’t expect these to be linked together. Nor is the access card we use to enter our office the same as the transit pass we use to board a bus. In the physical world, different transactions require different identity credentials, but they need not be linked together. It should be no different in the online environment.”
The next generation of intelligent and interactive web services (“Web 2.0”) will require more, not fewer, verifiable identity credentials, and much greater mutual trust to succeed.
Identity systems that are consistent with the Privacy-Embedded Laws of Identity will help consumers verify the identity of legitimate organizations before they decide to continue with an online transaction.
These Privacy-Embedded Laws offer individuals:
- easier and more direct user control over their personal information when online;
- enhanced user ability to minimize the amount of identifying data revealed online;
- enhanced user ability to minimize the linkage between different identities and actions;
- enhanced user ability to detect fraudulent messages and websites, thereby minimizing the incidence of phishing and pharming.
Corresponding Privacy-Embedded Principles
Take, for example, Law #1, Personal Control and Consent, which emphasizes that individuals should be in full local control of their own identity information, and exercise informed consent over how their identity information is collected and used by others. One privacy benefit of applying this principle is that identity credentials could be stored locally and securely on a user’s own computer rather than in a centralized online database.
Another example: Law #2, Minimal Disclosure for Limited Use: Data Minimization, speaks to building technical identity systems that minimize the amount of identity information used and disclosed in a given online transaction. In the privacy world, a cardinal rule is that the identification provided should be proportional to the sensitivity of the transaction and its purpose. Why should a credit card number ever be used to verify one’s age? Put another way, why isn’t there a credential that allows people to prove they’re over 65 without revealing all of their other identity information? If someone can prove she is a bona fide university student to gain preferential access to online resources at other educational institutions, then why is her name needed? These privacy-enhanced solutions are all possible under the Privacy-Embedded Laws of Identity.
“We call upon software developers, the privacy community and public policymakers to consider the Privacy-Embedded Laws of Identity closely, to discuss them publicly, and take them to heart,” Dr. Cavoukian declared. “In joining with us to promote privacy-enhanced identity solutions at a critical time in the development of the Internet and e-commerce, both privacy and identity/security will more likely be strongly protected.”
The Information and Privacy Commissioner is appointed by and reports to the Ontario Legislative Assembly and is independent of the government of the day. The Commissioner's mandate includes overseeing the access and privacy provisions of the Freedom of Information and Protection of Privacy Act and the Municipal Freedom of Information and Protection of Privacy Act, as well as the Personal Health Information Protection Act, and helping to educate the public about access and privacy issues.
Additional Resources:
7 Laws of Identity: The Case for Privacy-Embedded Laws of Identity in the Digital Age
The LAWS OF IDENTITY The key to this site: an introduction to Digital Identity – the missing layer of the Internet.
The IDENTITY METASYSTEM A proposal for building an identity layer for the Internet
Labels: cardsystems, health information, identity theft, ontario, phipa, privacy
Monday, August 28, 2006
Ontario Commissioner finds that CIA does not have access to health information
I blogged yesterday about the controversy surrounding an indirect CIA investee company providing services to Canadian health providers (Canadian Privacy Law Blog: Privacy groups slam use of CIA-backed software to index Canadian health files). The Information and Privacy Commissioner of Ontario just issued an investigation report ((PHIPA Report HI06-45) and the following media release in response:
CNW Group:Electronic health information strongly protected in Ontario: Commissioner Cavoukian
TORONTO, Aug. 28 /CNW/ - An investment in Initiate Systems Inc., a company providing software to an electronic health record application in Ontario, does not provide the CIA or anyone else with access to personal health information, says Dr. Ann Cavoukian, Ontario's Information and Privacy Commissioner.
In March 2006, In-Q-Tel, the venture capital arm of the CIA, invested in Initiate Systems Inc., whose software is being used in provincial electronic health record applications across Canada under an agreement with Canada Health Infoway, a federally funded, non-profit corporation that leads electronic health initiatives in Canada.
Prior to In-Q-Tel's investment, Initiate Systems' software was selected for use in one application in Ontario - the Enterprise Master Patient Index (EMPI). Although the EMPI contains health card numbers and other identifying information, it does not include diagnoses, prognoses, or other clinical information typically shared between health care providers and their patients. In Ontario, the Personal Health Information Protection Act establishes rules for the collection, use and disclosure of personal health information and designates the Office of the Information and Privacy Commissioner/Ontario as the body responsible for overseeing compliance with the legislation.
On August 11, 2006, privacy advocates expressed concerns that In-Q-Tel's investment in Initiate Systems may give the CIA access to provincial medical records. Commissioner Cavoukian immediately launched a privacy investigation into the allegations to determine if any personal health information was being disclosed in contravention of Ontario's health privacy legislation.
Among the Commissioner's findings in her investigation report:
- Cancer Care Ontario, which operates the EMPI on behalf of the Ministry of Health and Long-Term Care, allows Initiate Systems Inc. extremely narrow, on-site access to personal health information, under tightly controlled and limited conditions, and only as necessary to enable Initiate Systems Inc. to provide the services that it is contractually obligated to provide;
- No health information from the EMPI flows outside of Ontario;
- In-Q-Tel's investment in Initiate Systems Inc. does not allow In-Q- Tel to access any health information contained in the Ontario EMPI.
"Cancer Care Ontario, an organization that my office has worked with on privacy issues since the implementation of the Personal Health Information Protection Act nearly two years ago, has an extensive array of privacy safeguards in place," said Commissioner Cavoukian.
In addition to written privacy, confidentiality and security provisions in the Master Software License and Services Agreement with Initiate Systems Inc., other safeguards include:
- Initiate Systems does not have any remote access to EMPI data and performs all technical support for the EMPI in Ontario, with comprehensive security measures in place;
- Access to the EMPI by Initiate Systems' staff must be authorized and verified by CCO and may only occur on its Ontario premises; and
- Initiate Systems is prohibited from disclosing EMPI data to any party without the prior written consent of CCO, which has neither been sought nor granted.
Looking further ahead, Commissioner Cavoukian makes three recommendations in her investigation report, which is posted on the IPC's website: www.ipc.on.ca.
RECOMMENDATIONS
1. The Commissioner should be consulted concerning any proposed amendments or changes to the confidentiality or privacy obligations contained in the agreement between CCO and Initiate Systems.2. The MOHLTC or any other person who operates the EMPI in the future should advise the Commissioner if there is a breach of the confidentiality or privacy obligations of the agreement by Initiate Systems, and the steps taken to mitigate the breach, the measures taken to prevent subsequent breaches, and the manner and nature of the notification provided to individuals whose personal health information is contained in the EMPI.
3. The MOHLTC or any other person who operates the EMPI in the future using the Initiate Software should advise the Commissioner when changes will be made to the source code for the Initiate Software, as well as the nature and rationale for these changes.
The Information and Privacy Commissioner is appointed by and reports to the Ontario Legislative Assembly, and is independent of the government of the day. The Commissioner's mandate includes overseeing the access and privacy provisions of the Freedom of Information and Protection of Privacy Act, the Municipal Freedom of Information and Protection of Privacy Act, and the Personal Health Information Protection Act, and helping to educate the public about access and privacy issues.
For further information: Media Contact: Bob Spence, Communications Co-ordinator, Direct line: (416) 326-3939, Toll-free: 800-387-0073, Cell phone: (416) 873-9746, bob.spence@ipc.on.ca
Labels: breach notification, cardsystems, health information, ontario, phipa, privacy
Wednesday, August 23, 2006
Privacy hall of shame
Wired News: Privacy Debacle Hall of Fame10. ChoicePoint data spill
9. VA laptop theft
8. CardSystems hacked
7. Discovery of data on used hard drives for sale
6. Philip Agee's revenge
5. Amy Boyer's murder
4. Testing CAPPS II
3. COINTELPRO
2. AT&T lets the NSA listen to all phone calls
1. The creation of the Social Security Number
The Wired article has more details on each of the above blunders.
Via Concurring Opinions and Rob Hyndman.
Labels: cardsystems, choicepoint, laptop, privacy
Tuesday, July 04, 2006
Victim impact statement on debit card fraud
A colleague in Alberta recently sent me a link to a recent case from Alberta, R. v. Singh, 2006 ABPC 156. It is a decision of the Alberta Provincial Court determining the appropriate sentencing for an individual who pleaded guilty to debit card fraud under section 342.1 of the Criminal Code of Canada. The decision is interesting in that it describes the crime in some detail, but the most interesting part is the victim impact statement submitted by the Interac Association:
“I, Fred Harris have been employed by INTERAC ASSOCIATION as Senior Vice President of Strategy and Business Development for over 15 years. In my capacity as Senior Vice President, I have knowledge of the fraud prevention mechanisms implemented by Interac Association’s member institutions to ensure the security of transactions on the Shared Cash Dispensing and Interac Direct Payment services (the “Interac Services” or the “Services”), and also of the specific matters addressed below.INTERAC SERVICES IN CANADA
The Interac Services account for millions of automated banking machine and payment transactions (known as “debit at the point of sale” or “POS” transactions) on a daily basis. These services enjoy a high degree of consumer confidence given the ease of use and the widespread acceptance of debit cards at locations ranging from retail outlets to federal and provincial government offices.
In 2004, there were 19.8 million users of Interac Direct Payment each month resulting in a total of 2.8 billion point of sale transactions. Those 2.8 billion transactions represent $124.4 billion dollars at 546, 000 point of sale terminals. In 2004, cardholders withdrew cash from an automated banking machine that did not belong to their own financial institution over 294 million time utilizing one of the 46,178 ABMs available in the Canadian marketplace. In addition to the transactions processed through the Interac Services there are close to one billion proprietary transactions, such as bill payments and cash withdrawals, processed on Members; own proprietary banking machines every year. These services are among the most secure in the world. Interac Association and its Members take extreme care in identifying threats and vulnerabilities to ABM or Point of Sales locations. Establishing stringent device level security standards, and by employing security features that can include surveillance cameras, and automated fraud detection systems.
Banking machine and point of sale transactions require a two factor authentication system consisting of the electronic reading of valid magnetic strips information from the back of a debit card plus the inputting of an associated Personal Identification Number (PIN). In recent years, criminals have developed diverse and increasingly ingenious means of obtaining the information on the magnetic stripe and PIN information from cardholders. This activity, often called “skimming” uses methods that range form low-tech ploys consisting of double swiping a cardholder’s card and then looking over the individual’s shoulder as the PIN is entered, to higher-tech methods that include hidden pinhole cameras and additional card readers installed on top of banking machine card readers or point of sale devices.
Once a skimming incident is identified, Interac Association and its Members take action to eliminate the source of skimming and manage the resulting exposure to cardholders and financial institutions. In order to protect cardholders, most exposed cards are proactively cancelled by the financial institution and the cardholder is notified that a replacement card is being required. Until the cardholder receives the replacement card they are unable to access their money using a banking machine or point of sale terminal. In other instances, thousands of cards are proactively blocked to stem losses, thereby increasing substantially the number of cardholders affected by a single skimming incident. Canadian financial institutions have been at the forefront of fraud prevention and detection and continue to develop improved procedures and use new technology as it becomes available.
THE IMPACT OF BANKING CARD FRAUD
The initial group affected by debit card fraud is [sic] cardholders. Money is taken directly from their chequing or savings accounts. In some cases cardholders are burdened in the short term by being unable to meet basis living requirements, for example they may be unable to make rent or mortgage payments. They may suffer immediate “on the spot” inconvenience and embarrassment, particularly given the widespread use and acceptance of debit cards, when their card cannot be used to pay for goods or other services. Cardholders must then take steps to lodge an inquiry with their financial institution, which leads to an investigation regarding the missing funds. Their financial institution will reimburse them if they are the victims of a proven fraud, but in the meantime they are inconvenienced.
In 2003 our Members collectively reimbursed $44 Million to approximately 28,000 cardholders who were victims of debit card fraud resulting from skimming. In 2004 this figure increased to $60 Million reimbursed to over 48,000 cardholders. The related costs are also significant. The time and effort to investigate each instance of fraud is a significant burden on the time and resources of law enforcement agencies, Interac Association, and the involved financial institutions, terminal deployers and merchants. Each incident typically requires a team of individuals from several different financial institutions and terminal deployers to retrieve and scrutinize various records and to liaise with the appropriate law enforcement agencies. This investigation often takes several weeks. In addition, financial institution often proactively block and re-issue other debit cards used at this location during the skimming period in order to prevent further losses. This represents a further cost to the financial institution as well as an inconvenience to cardholders.
Interac Association and its Members, and the entire industry, also suffer. At a minimum, debit card fraud shakes customer confidence in the use of modern banking technology. This risk and potential harm increase exponentially when one considers that criminals often share the success of their schemes on readily accessible internet bulletin boards.”
Labels: alberta, cardsystems, privacy, surveillance
Saturday, June 10, 2006
The Practical Nomad on the Expedia/Hotels.com data breach
The Practical Nomad has a very interesting post on the recent Expedia/Hotels.com privacy and security breach resulting from the loss of an auditor's laptop. (For my previous comments, including the fact that my data may have been on the laptop in question, see: The Canadian Privacy Law Blog: Incident: Hotels.com customer info on laptop stolen from auditor in February.)
The Practical Nomad blog: Expedia auditors lose laptop with customer credit card numbers:
...
Notably, Expedia has not said whether it had in place the contractual privacy commitments from Ernst & Young that would be required under Canadian (and other countries') laws -- although not under USA law -- as a precondition to allowing Erndst & Young to access personal information in customer or reservation records.
Hotels.com operates one of the world's largest travel Web site affiliate networks , many of whose members (in addition to the other Expedia divisions in the USA, Canada, and Europe), hide the Hotels.com service behind their own "private label". Many Hotels.com customers may never have realized they were dealing with Hotels.com rather than the company that operates the "private label" Web site. In the past, this lack of transparency has been one of the major themes of customer compliants against Hotels.com, especially when customers had problems at check-in and didn't knom whom to call. And customers of Expedia divisions in Canada and Europe may not have known that their personal data was being passed on to Hotels.com in the USA.
So, I asked, (1) does Hotels.com attempt to identify, or keep a record of, the country from which personal information was collected, and (2) are the actions being taken the same for all people whose data may have been on the stolen laptop, or are any different or additional actions being taken with respect to people from whom data may have been collected while they were in Canada or the European Union (e.g. as potentially identifiable from the IP address or the origination of the transaction through Expedia.ca or Expedia.uk), in light of the differences in Canadian and European Union data protection law?
The response on behalf of Expedia? "We do not track or capture geographies aside from the address customers provide for the transaction."
In other words, the word's largest Internet travel agency -- even though it requires cookie acceptance for purchases, and undoubtedly logs IP addresses and tracks referrals by affiliate -- make no attempt to keep track of the jurisdiction and legal conditions under which personal information is provided, or ensure that those restrictions accompany the data whenit is passed on. Even if they wanted to comply with the law in Canada and the EU, where they operate entire divisions, their current data structures aren't adequate to support compliance with the laws in those jurisdictions.
From what I've seen of industry norms, Expedia is no exception. Neither computerized reservation systems nor the AIRIMP (more on the latest AIRIMP revisions in a forthcoming post) support transmitting or recording the jurisdiction or rules under which any portion of the data in a passenger name record (which typically includes data entered in multiple jurisdictions, so a single field for the entire PNR would not suffice). But if Expedia can get away with ignoring data protection laws in countries where they do billions of dollars a year in busisness, so can the little guys.
This should be the test case of whether USA-based travel companies that do business in, and/or accept personal data from affiliates in, Canada and the EU need to track the jurisdiction and conditions governing use of that data, and ensure that those jusirsdictional and usage-restriction notes follow the data wherever it goes.
If you reserved a hotel through Hotels.com, and you were in Canada or the EU at the time, demand an explanation from the company, and complain to your national privacy commissioner or other national data protection authorities.
Labels: cardsystems, information breaches, ip address, laptop
Sunday, March 19, 2006
Debit card breach traced to POS systems
More information about the problems that may underly the recent and significant payment card breach is starting to come in. ZDNet is reporting that Visa has sent a bulletin retailers, warning that a certain brand of point-of-sale equipment may retain personal information, including PINs.
Visa warns software may store customer data Tech News on ZDNetA popular software that retailers use to control debit-card transactions may inadvertently store sensitive customer information, including PIN codes, says Visa.
Two versions of cash-register software made by Fujitsu Transaction Solutions are under scrutiny, according to a warning Visa issued to the companies that process card transactions for some of the nation's largest retailers. A Visa representative confirmed that the warning was sent.
Some of Fujitsu's retail customers include Best Buy, Staples and OfficeMax, but it is not known which companies use the software Visa claims is flawed.
Visa's warning, which was first reported by The Wall Street Journal on Friday, has raised eyebrows in the financial and retail sectors. The software was flagged at a time when thousands of debit-card holders across the country have reported unauthorized withdrawals from their accounts.
Thanks to Slasdot for the pointer.
Labels: cardsystems, information breaches, retail
Saturday, February 25, 2006
Cardsystems settles with the FTC
The US Federal Trade Commission has settled its complaint against CardSystems after a breach at the company comproised the personal information for forty million credit and debit card users. The company had, against its agreement with the card-issuers, kept information related to transactions it was processing and failed to secure it adequately.
Somewhat oddly, the LA Times article says that the FTC could not levy any civil damages or penalties, as it did with ChoicePoint, without mentioning why.
CardSystems Settles ChargesFrom Associated Press
February 24 2006
WASHINGTON — A data breach that left 40 million customer accounts vulnerable to hackers will lead to tighter security measures to protect millions of credit and debit card users, Federal Trade Commission officials said Thursday.
CardSystems Solutions Inc. has settled charges that the company broke the law by failing to ensure adequate safeguards for sensitive customer information. The breach resulted in millions of dollars in fraudulent purchases, the commission said.
The settlement calls for better safeguards to protect consumer data.
The FTC could not seek civil penalties under the law it accused CardSystems of violating.
Atlanta-based CardSystems processed credit card and other payments for banks and merchants. Last summer, it was disclosed that tens of millions of mostly MasterCard and Visa accounts were exposed to possible fraud after a hacker broke into the company's computer system.
"CardSystems kept information it had no reason to keep and then stored it in a way that put consumers' financial information at risk," FTC Chairwoman Deborah Platt Majoras said.
CardSystems' assets have since been bought by San Francisco-based Pay by Touch. The settlement requires Pay by Touch to implement a comprehensive security program and obtain independent audits every other year for 20 years.
Labels: cardsystems, choicepoint, information breaches
Tuesday, December 20, 2005
Data Privacy Issues to Persist Next Year
On the data privacy front, the new year will bring more of the same, according to eWeek:
Data Privacy Issues to Persist Next Year:"People may remember 2005 as the year that corporate America woke up to the problem of data breaches and the importance of data privacy. Data leaks at Bank of America Corp., LexisNexis' Seisint division, ChoicePoint Inc. and CardSystems Inc. fed headlines for months, spawned countless lawsuits on behalf of aggrieved consumers and provided the impetus for federal legislation--still pending--to protect consumer data. But what will 2006 bring?
More of the same, say leading security experts.
More than ever before, enterprise IT managers will have to fight a battle on two fronts next year. On one side, more sophisticated and targeted attacks from organized, online criminal groups will test networks in new ways that are hard to detect...."
Labels: cardsystems, choicepoint, information breaches
Monday, December 12, 2005
Incident: Security breach at Sam's Club exposes credit card data
From Computerworld:
Security breach at Sam's Club exposes credit card data - ComputerworldDECEMBER 12, 2005 (COMPUTERWORLD) - Sam's Club, a division of Wal-Mart Stores Inc., is investigating a security breach that has exposed credit card data belonging to an unspecified number of customers who purchased gas at the wholesaler's stations between Sept 21 and Oct. 2. In a brief statement released Dec. 2, the Bentonville, Ark.-based company said it was alerted to the problem by credit card issuers who reported that customers were complaining of fraudulent charges on their statements.
It's still not clear how the data was obtained, according to the statement. But "electronic systems and databases used inside its stores and for Samsclub.com are not involved," the company said.
Sam's Club is currently working with both Visa International Inc. and MasterCard International Inc. to investigate the breach. The company also has notified the U.S. Attorney's Office for the Western District of Arkansas and the U.S. Secret Service .
Sam's Club officials didn't respond to calls for comment.
In a statement, Visa said it has alerted all of the affected financial institutions, asked them to provide independent fraud-monitoring services to affected customers and requested that they issue new cards as needed.
Labels: cardsystems, information breaches
Sunday, December 11, 2005
Cardsystems acquisition closes
The acquisition of Cardsystems by Pay by Touch announced in October (The Canadian Privacy Law Blog: Another suitor for CardSystems) has been concluded, according to a release issued on Friday: Pay By Touch Completes Acquisition of CardSystems Solutions: Financial News - Yahoo! Finance.
For those who may have forgotten, Cardsystems was involved in a high-profile data breach earlier this year: The Canadian Privacy Law Blog: Incident: Security Breach at CardSystems Solutions Inc. Could Expose 40M to Fraud.
Labels: cardsystems, information breaches
Wednesday, December 07, 2005
Cornell University outlines security and privacy incident response plans
In response to a new New York law that requires notification of security and privacy breaches, Cornell University has issued the following media release outlining their plans for compliance:
Cornell complies with new state law on notification about stolen data:By Bill Steele
If someone hacks into a Cornell University computer and pulls out personal and private information about members of the Cornell community, the people whose data has been compromised will be notified promptly, according to Cornell Information Technologies and the University Counsel's office.
Although the exact procedures have not been worked out, notification would be by ordinary mail, according to Norma Schwab, associate university counsel. E-mail notification, she said, is not legally adequate and might be unreliable, especially in an age when users are bombarded with "phishing" messages with subject lines like "your account has been compromised."
The notification plan is being developed by an ad hoc group called the Data Incident Response Team, which includes members from the Office of Information Technologies, the Office of University Counsel, Cornell Police and the University Audit Office. The group meets periodically to consider data security policy and comes together whenever there is a concern that sensitive data may have been accessed.
The action is in response to a New York state law, the Information Security Breach and Notification Act, passed in August and going into effect Dec. 8. The law requires any business -- including nonprofits -- that maintains personal and private data to provide notification when its systems are invaded and there is a reasonable belief that personal information might have been revealed. The kinds of data involved include Social Security and driver's license numbers and credit card information, and the notification requirement is intended to help consumers fend off possible identity theft.
"It made sense that we should let people know that we are complying with the new law," said Steve Schuster, director of information security. Schuster said he plans to take advantage of the opportunity to make Cornell staff more aware of their responsibilities to protect sensitive data.
"We're still in a state where our data resides in a lot of different areas," he explained. "We all have to take responsibility for it." In other words, sensitive information is not all on one university mainframe, but may also be on ordinary desktop computers in various departments. Schuster plans to require that all new staff members receive a policy and practices briefing -- a short version of the Travelers of the Electronic Highway course required for new students -- before they are issued net IDs. He hopes eventually to set up some sort of annual review of security procedures for all staff. For nontechnical staff, security measures include using strong passwords, protecting those passwords from disclosure and physically securing the computer.
University policies on security are being updated. The venerable Responsible Use of Electronic Communications policy is being expanded as Responsible Use of Information Technology Resources, and it will incorporate policies on data management and security. Data will be broken into three categories: regulated information for which state and federal laws require security, such as Social Security numbers and grades; "Cornell confidential" information, such as salaries and performance reviews; and public data. Security should be tailored to the level of confidentiality of the data. "It will be necessary for departments to inventory where these data reside in their systems," Schuster said.
Despite having very talented people around, higher education institutions are not immune to security breaks, Schuster pointed out. "In the first six months of 2005 there were 72 media-worthy computer compromises in the United States," he reported, "and slightly over half of them were in higher ed. We deal with break-ins here all the time, but we have a really good process in place."
The New York law, patterned on one passed about two years ago in California, was inspired by several incidents in which large corporate databases were compromised. In the most widely publicized case, ChoicePoint, a credential-verifying firm, allowed criminals to obtain personal data on some 140,000 people. At least 15 states have passed similar laws, and legislation is pending at the federal level.
Labels: breach notification, cardsystems, choicepoint, identity theft, information breaches
Thursday, November 03, 2005
Wisconsin reissues cards after CardSystems breach
The largest bank based in Wisconsin has replaced a number of customers' debit and credit cards after the high-profile CardSystems breach: JS Online: M&I reissues credit, debit cards.
Labels: cardsystems, information breaches
Tuesday, October 25, 2005
CardSystems class action update
The pre-trial process in the Cardsystems class action lawsuit continues, while the parties are squabbling over what and how much information Visa and MasterCard should be providing to the plaintiffs about their relationships with Cardsystems: Squabble continues over credit card breach | Tech News on ZDNet.
Labels: cardsystems, information breaches, tort
Sunday, October 16, 2005
Another suitor for CardSystems
First, CardSystems was circling the bowl: CardSystems threatened with extinction due to Visa and AMEX termination.
Then, CardSystems was being bought by CyberSource: Cardsystems assets being sold to CyberSource.
Then, CyberSource leaves CardSystems at the altar: CyberSource Terminates Negotiations with CardSystems.
Now, CardSystems is being wooed by Pay by Touch: Card Center Hit by Thieves Agrees to Sale (registration req'd).
Labels: cardsystems, information breaches
Saturday, October 15, 2005
CyberSource Terminates Negotiations with CardSystems
A press release put out today says that Cybersource has withdrawn its offer to purchase embattled CardSystems: CyberSource Terminates Negotiations with CardSystems: Financial News - Yahoo! Finance.
See, also, The Canadian Privacy Law Blog: Cardsystems assets being sold to CyberSource, et seq.
Labels: cardsystems, information breaches
Tuesday, October 04, 2005
Visa delays plan to cut ties with CardSystems
Hot on the heels of the announcement that CyberSource was planning to acquire CardSystems, VISA USA now says it will delay by three months its planned termination of its relationship with CardSystems. This may ultimately lead to the survival of the embattled transactions processor: Visa delays plan to cut ties with CardSystems - Computerworld.
Labels: cardsystems, information breaches
Monday, September 26, 2005
Effect of privacy/security incidents on stock prices
Kenneth Belva, a New York-based information security officer, has written an interesting review of the effect of privacy and security breaches on the stock prices of the companies involved (How It's Difficult to Ruin A Good Name: An Analysis of Reputational Risk). The purpose of the report is to "begin the conversation", but it does note some interesting trends: the closer privacy and security is to your core business, the greater the impact upon stock prices.
"In the cases were there was a temporary loss or no loss at all [in share price], it appears that the breach was not in an area that effected [sic] the core business. In other words, even though Citigroup and UPS lost 3.9 million customer records, Citigroup was still able to lend money and UPS could continue shipping packages.I am willing to leave an open hypothesis on the table: The greater the financial impact or potential financial impact from the information security incident, the greater the reputational damage; the less the financial impact or potential financial impact from an information security incident, the less the reputational damage."
I might add something to the conversation (which I am basing only on my gut): consumers are more fickle than companies and companies are more afraid of the bad reputation of associated companies rubbing off on them. A credit card issuer won't get a big hit when one of their service providers loses data, but it is very easy and likely prudent for the credit card company to cut the service provider loose. If a company like CardSystems loses contracts with two of three major credit card issuers, that's the death of the company. The further down the chain you go, the greater the impact of these incidents. It makes sense if you look at the impact of these incidents on potential revenues: the person at a credit car company who recommends service providers has a number of companies to choose from, puts her personal reputation on the line when she recommends a provider and does due diligence on all prospective providers. A provider with a big blemish sticks out and doesn't get chosen. Consumers as a group are less discerning than the handful of people who make business-critical decisions. Simply put, if you are a critical service provider to other businesses, your reputation matters more.
Also, as Belva points out in his report, stock price may not be the only indicator of the hit companies take if they are associated with a privacy/security incident. It is just the most visible measure.
Greg Keizer at Information Week has an article on Belva's report that's worth reading: InformationWeek > Security > Report: Security Slip-Ups Don't Ding Stock Prices For Long > September 23, 2005.
Labels: cardsystems, information breaches
Friday, September 23, 2005
Cardsystems assets being sold to CyberSource
CyberSource, a California-based electronic transactions company, has announced that it signed a letter of intent to buy the assets of embattled Cardsystems. The sale is supposed to close sometime in the fourth quarter of this year and the likely purchaser is in talks with Visa and Amex to take over the transactions that are slated to be terminated in October due to the high-profile security breach at Cardsystems. See: CyberSource seeks to buy CardSystems.
Labels: cardsystems, information breaches
Credit card companies head to court over disclosure obligation
According to Wired News, both Visa and Mastercard are planning to argue in a Cardsystems-related lawsuit that the card associations do not have an obligation to notify individuals of security and privacy incidents. If there is an obligation, it falls to the member banks who have the immediate relationship with the customers. Interesting question: Wired News: Card Companies Keep Theft Quiet.
Labels: cardsystems, information breaches
Monday, September 05, 2005
Embattled Cardsystems submits audit report to credit card companies
On Thursday, the embattled CardSystems submitted an audit of its practices to Visa, Mastercard and American Express in hopes of ensuring the survival of the company. According to the Arizona Daily Star, Visa has been pursuaded by an Arizona congressman to reconsider its decision to cut ties with Cardsystems: CardSystems hopes audit will help.
For previous postings about CardSystems, click here.
Labels: cardsystems, information breaches
Thursday, August 04, 2005
Court orders data on credit card heist to be saved
As part of a class-action lawsuit brought against CardSystems Solutions Inc, the Superior Court of California has ordered the payment processor to preserve the data associated with the high-profile breach, according to CNet News:
Court orders data on credit card heist to be saved | CNET News.com:"A California court on Tuesday ordered CardSystems Solutions, Merrick Bank, Visa and MasterCard to preserve data related to the security breach at CardSystems, a payment processing company. Additionally, the Superior Court of the State of California in San Francisco set an Aug. 17 date for a hearing on the issue of informing individual credit card holders if their card data was exposed in the breach...."
Labels: cardsystems, information breaches
Tuesday, August 02, 2005
Analysts Say ATM Systems Highly Vulnerable
The Associated Press is reporting on a report from Gartner Inc., which suggests that most banks are not doing enough to protect customers from ATM fraud. The reason is that most bank and debit cards do not take advantage of the full potential of two-track magnetic strips. Most bank cards only encode the card number on the magnetic strip, so anybody with a card writer and your card number (available from discarded receipts) is able to make a duplicate. Combine that with your PIN and that's the key to emptying your account. The solution posited by the Gartner analysts is to use the second track in the magnetic strip to encode an additional token that is verified by the ATM but is not otherwise available to the users. Some banks already use this technique. See: Analysts Say ATM Systems Highly Vulnerable - Yahoo! News.
Labels: cardsystems, information breaches
Monday, August 01, 2005
The CardSystems blame game
First, blame the auditors ...
Mark Rasch, in his Security Focus column this week, has some interesting things to say about security auditors and consultants in the wake of the cardsystems breach. The focus of his column is on what audits are and are not, but also contains some interesting insights about the Cardsystems debacle.
The CardSystems blame game"...None of this is surprising. One of the first things you do when confronted with a public relations problem is to minimize the extent of the problem. Lawyers do this all the time, exclaiming things like "My dog didn't bite you, my dog doesn't bite, I don't own a dog." The next thing to do, of course, is to find someone else to blame.
In the case of CardSystems, they reportedly found someone who wasn't at the table to blame -- not VISA, not MasterCard, not their sponsoring bank, and not their customers. They blamed their auditors and consultants. In his testimony, Perry noted that CardSystems had undergone a CISP audit by consultants from Cable and Wireless in December of 2003 (17 months before the incident), and that there were "do deficiencies" that did not have adequate compensating controls. Thus, according to Perry's live testimony, it was Cable and Wireless' fault. Oh, and while he was at it, he also reportedly blamed the California mandatory disclosure law, SB 1386, claiming that without the law, the company would have suffered no losses. Well, still the data would have been lost, just nobody would have known about it.
Cable and Wireless claimed that there was nothing wrong with their audit, and that they were simply retained to audit the systems that were used to process the payment information. If there was a separate system used to store transactional data not connected to the processing system, or a system not within the scope of the audit, it was not examined.
Meeting of the minds
The relationship between consultant and consultee is almost always one based on a consulting agreement. The case points out a serious problem with understanding the nature of auditors, security consultants, and the relationship between these consultants and the underlying client. The consulting contract is supposed to reflect a meeting of the minds between the parties. Invariably however, the parties come to the table with differing expectations about what they are buying and selling. In the case of CardSystems and Cable and Wireless, CardSystems thought they were auditing discrete parts of the payment processing network for compliance with VISA's standards. CardSystems, on the other hand, apparently thought they were purchasing "hacker insurance" and a guarantee that they would never be subject to attack. At a minimum, CardSystems was seeking a "Certificate of Assurance" that they were compliant with all the relevant standards. As we will see, even this latter assumption may be unrealistic...."
Labels: cardsystems, information breaches
Learning the ABCs of identity theft
The Daily Herald of Provo, Utah has a Q & A column. This week, it's about identity theft:
Learning the ABCs of identity theft :: The Daily Herald, Provo Utah Learning the ABCs of identity theft"Q: Do all of the recent data thefts mean everyone affected will be a victim of identity theft? How can one protect oneself against identity theft if our data isn't safe? -- MT, Palo Alto, Calif.
A: The theft of data is in the news almost every day. It would seem that, based on the recent rash of data thefts, almost the entire country is now exposed to identity theft.
...
The root cause of the recent data thefts are companies and organizations -- banks, credit card processors, universities, motor vehicle departments and Web sites -- that maintain a great deal of sensitive personal information in their databases. Their databases are constantly hacked, and these companies lack the appropriate level of standards with respect to protecting data.
Your question is certainly timely and provides an opportunity to review the basics of identity theft.
As explained before, identity theft is a crime that occurs when a thief steals your personal information and then uses it to impersonate you or to commit fraud and theft in your name. Typically, the thief will need your Social Security number, your name, address and driver's license in order to "become" you. In certain cases, the thief may also need your credit card account numbers and other information contained in your credit report.
...
In this context, you need to understand the difference between identity theft and credit card fraud. When, for example, a security breach at CardSystems Solutions compromised 40 million credit cards, you likely became exposed to credit card fraud, not identity theft.
Credit card fraud, while annoying and troubling, does not expose you to the same effects as identity theft. Federal law limits your financial risk to $50...."
Labels: cardsystems, identity theft, information breaches
Friday, July 29, 2005
CardSystems made its choices clear
The chorus in favour of stronger privacy protections is getting louder. Daniel Handson, at SecurityFocus, has written an opinion piece at that website, calling for greater laws to deal with incidents like the CardSystems breach:
CardSystems made its choices clear"... The latest news in this escapade is that CardSystems has now lost the contracts it had, and also faces corporate extinction. Now some reading this may be cheering a little, or perhaps a lot, at the karmic balance of CardSystems potentially paying the ultimate price for their cavalier attitude. However other people are suggesting that this corporate extinction might come as a result of misguided notification laws implemented in California, and that without the mandated public disclosure and the resulting firestorm of controversy, the company could have fixed its problems quietly and kept on serving its shareholders and customers. I think that both of these views are misguided and miss the truth.
CardSystems violated a contractual agreement that was put in place by the companies it served. It's that simple. CardSystems kept data in an insecure fashion, with no concern given to the minimum security and encryption standards that it was required to implement. I fail to see why legislation on data protection would change this situation. CardSystems was already required to maintain a certain level of security and failed to do that. In one report, Bruce Schneier, mentioned that this was a common problem with contractual obligations: the fact that auditing is hard. Therefore I cannot see why changing a contractual agreement into a legislated law will make auditing any easier. To draw another comparison, did the fact that they were violating laws affect the behavior of the people at Enron?
Many companies have a long way to go in the security world, and yet the one sector of our civilian society that tends to get information security is the banking and financial industry. Sure they aren’t perfect, but in my experience they are heads and tails better than almost anyone else that I deal with at understanding data privacy. In the case of CardSystems, however, the industry insisted that minimum standards be maintained, outlined what those minimum standards were, and yet much of that was ignored. CardSystems, if it does go bankrupt, will have done so because they willfully violated a contractual obligation, not because of disclosure laws, or public pressure. Would you use a company that had willfully violated previous contracts? Would you want your credit card company to supply your data to that company? I cannot see why repealing disclosure laws and helping to mitigate the lynch mob mentality that can follow a mistake changes the fact that CardSystems violated a contract, and that contract violation is what has brought about this imminent death. I await the forthcoming laws that attempt to prevent something like this from ever happening again. Meanwhile, I continue to check my credit-card statement, bank statements and never give out my Social Insurance Number (or SSN) unless I absolutely have to. I wonder if any of the legislators who are outraged by this would give me their mother’s maiden name, birth-date and the name of their first pet? ..."
Labels: breach notification, cardsystems, information breaches, schneier
Monday, July 25, 2005
Lawsuits broach data-security breaches
Journal Gazette | 07/25/2005 | Lawsuits broach data-security breaches"... The Marin County, Calif., salesman, along with two other plaintiffs, has filed a class-action lawsuit in California Superior Court in San Francisco against CardSystems Solutions Inc., which last month acknowledged that hackers had obtained information on approximately 200,000 credit- and debit-card accounts. The payment-processing concern might have put the personal information of as many as 40 million consumers at risk, including Schultz’s Visa debit-card account.
Schultz, 52, hasn’t discovered fraudulent activity in connection with his Visa account; and even if he wins, he isn’t likely to recoup much money for the time and trouble of monitoring his account and changing his automatic-payment arrangements.
But his suit against CardSystems, of Tucson, Ariz., might help answer one of the biggest questions arising from the recent rash of data-security breaches: Who should pay for damages?
In an earlier era, when little was known about particular hackings, accountability was difficult and data losses were deemed an unavoidable annoyance. Now, merchants, banks, payment processors, credit-card associations and even security auditors and software makers face the prospect of liability for lax practices.
“There is going to be a flood of lawsuits by both consumers and businesses,” said Mark Rasch, a former Justice Department prosecutor and now senior vice president for Solutionary Inc., a security-audit firm in Bethesda, Md. ..."
Labels: cardsystems, information breaches, tort
Saturday, July 23, 2005
Changing credit card numbers won't help
Over at Schneier on Security, there's been a bit of a discussion in the comments about how to deal with the increasingly reported security incidents involving credit card processors. One commentator suggested a novel approach to protecting his own accounts:
Schneier on Security: Visa and Amex Drop CardSystems:"Me? I request replacement credit and debit card numbers every six months, and watch my account activity carefully."
Interestingly, Dr. Don at Bankrate.com just fielded a question on the practice:
Changing credit card numbers won't help:"Dear Kim,
Your idea about rotating credit card numbers is inventive but it could actually wind up increasing the odds that you find yourself a victim of identity theft or credit card theft. Getting a new credit card number every quarter would mean that you will have credit cards in your mailbox four times a year vs. once every three to four years, and fraud programs that recognize when your spending patterns don't jibe with past purchases aren't going to be effective, because the account won't have a transaction history for comparison.
It's also likely to hurt your credit rating because your credit history will show a series of accounts closed at your request every three months -- unless the series of account numbers is treated as a single account relationship by the credit card provider. For this to happen it would have to be a practice established by the credit card provider in reporting your history to the credit bureaus. It isn't something that you can do on your own...."
Labels: cardsystems, identity theft, information breaches, schneier
Friday, July 22, 2005
CardSystems threatened with extinction due to Visa and AMEX termination
The CEO of CardSystems testfied before the US House Financial Services Subcommittee that his company is likely to shut down because Visa and Amex is ending their relationship with the company that was faulted with allowing a breach of personal information of 40M people.
Credit Data Firm Might Close - Yahoo! News:"As a result of coming forward, we are being driven out of business," John M. Perry, chief executive of CardSystems Solutions Inc., told a House Financial Services Committee subcommittee considering data-protection legislation. He said that if his firm is forced to shut down, other financial companies will think twice about disclosing such attacks. ...
Perry called the decisions by Visa and American Express draconian and said that unless Visa reconsiders, CardSystems would close and put 115 people out of work. CardSystems handles only a small percentage of American Express transactions, while Visa accounts for a large part of its business.
Perry said closing his company could disrupt the ability of merchants to complete transactions, since it might take time for them to arrange for alternate payment processors. For that reason, Visa said it is not cutting off the company until Oct. 31.
While Perry said his company is doing everything it can to ensure that such a breach never occurs again, Visa said it could not overlook that CardSystems knowingly violated contractual requirements for how long credit card data were supposed to be stored and how they were secured...."
Labels: cardsystems, information breaches
![]()

The Canadian Privacy Law Blog is licensed under a
Creative Commons Attribution-Noncommercial-No Derivative Works 2.5 Canada License.